Read this in 30 seconds: SOC is your 24/7 security team monitoring threats in real time. VAPT is your periodic offense team finding vulnerabilities before attackers do. SIEM is the tool that collects and correlates all your security data. Most companies buy one and think they’re protected. They’re not. You need all three working together, and the SOC vs VAPT debate is a false choice that gets organizations breached. This guide breaks down exactly what each does, where they overlap, where they don’t, and how to build a complete security program without wasting budget on the wrong thing first.
Most companies treat cybersecurity like a buffet. They pick one thing, pile it on their plate, and call it a complete meal.
“We have a SIEM” is not a security program. “We did a pentest last year” is not a security program. And “we outsourced our SOC” doesn’t mean you can sleep at night.
The SOC vs VAPT debate is everywhere online and almost every article gets it wrong. They compare the two like you’re choosing between them. You’re not. That’s like asking “should I have brakes or a steering wheel in my car?” You need both or you crash.
But here’s what nobody explains properly: how SOC, VAPT, and SIEM actually fit together, which one to invest in first, and what happens when you skip any one of them.
Nobody’s doing the homework. So I did.
I’ve spent years building security operations, running VAPT engagements, and deploying SIEM platforms across production environments. This guide breaks down the SOC vs VAPT vs SIEM triangle the way it should have been explained from day one.
What Is a SOC, Really? Not the Marketing Version
A Security Operations Center (SOC) is your 24/7 security nerve center. That’s the textbook answer every vendor gives you before trying to sell you a $200k/year managed service.
Here’s what a SOC vs VAPT comparison actually looks like in practice: the SOC is your defense team sitting in the trenches, watching screens, triaging alerts, and responding to incidents in real time.
A SOC team operates in three tiers:
L1 Analysts monitor dashboards and triage incoming alerts. They’re your first line of defense. Most of their day is separating real threats from noise. And there’s a lot of noise.
L2 Analysts dig deeper into confirmed incidents. They investigate, correlate events across systems, and determine scope and impact.
L3 Analysts / Threat Hunters proactively search for threats that automated tools miss. They write detection rules, reverse-engineer malware, and do the work that actually keeps advanced attackers out.
The tools a SOC uses:
- SIEM platforms (we’ll get to that)
- EDR/XDR for endpoint visibility
- Threat intelligence feeds
- SOAR platforms for automation
- Network detection and response (NDR)
- Case management and ticketing
Here’s the thing. A SOC without good tools is just people staring at logs. And tools without good people are just expensive dashboards nobody reads.
The real value of a SOC isn’t the tools or the people individually. It’s the combination: trained analysts armed with proper visibility, responding to threats before they become breaches.
What Is VAPT? The Offense Side of Security
VAPT stands for Vulnerability Assessment and Penetration Testing. It’s two things packaged as one because the industry loves acronyms.
Let’s break them apart because in the SOC vs VAPT discussion, people constantly confuse what VAPT actually delivers:
Vulnerability Assessment (VA) is the automated scan. You point Nessus, Qualys, or OpenVAS at your network and it spits out a list of known vulnerabilities with CVE numbers and severity scores. It’s fast, it’s broad, and it tells you what could be exploited.
Penetration Testing (PT) is a human actively trying to break in. A pentester uses the vulnerabilities found during assessment (and ones the scanner missed) to simulate a real attack. They chain exploits, escalate privileges, move laterally, and prove actual impact.
Translation: VA tells you “your front door lock is weak.” Pentesting proves it by actually picking the lock, walking through your house, and leaving a note on your pillow.
Types of VAPT You Should Know About
| VAPT Type | What Gets Tested | When to Run | SOC vs VAPT Relevance |
|---|---|---|---|
| Network VAPT | Firewalls, servers, internal network | Quarterly | Feeds SOC with known weak points |
| Web Application VAPT | Websites, APIs, web apps | Before launch + quarterly | Finds what WAF rules miss |
| Mobile VAPT | Android/iOS apps | Before each release | Separate from SOC scope |
| Cloud VAPT | AWS/Azure/GCP configs | Semi-annually | Critical for cloud SOC visibility |
| API VAPT | REST/GraphQL endpoints | With every major API change | APIs are the #1 blind spot |
| Social Engineering | Phishing, vishing, physical | Annually | Tests SOC’s human-layer detection |
The critical difference people miss in the SOC vs VAPT comparison: VAPT is periodic. You run it quarterly, semi-annually, or before launches. A SOC runs 24/7/365. VAPT finds problems. SOC watches for exploitation of those problems (and new ones) in real time.
They’re not alternatives. They’re two halves of the same equation. Anyone presenting SOC vs VAPT as an either/or choice is selling you something.

What Is SIEM? The Brain Behind the Operation
SIEM stands for Security Information and Event Management. It’s the technology that makes your SOC actually functional.
Think of it this way: if the SOC is your security team, the SIEM is their brain. Without it, they’re just people with no data. With it, they can correlate events across your entire infrastructure, spot patterns that no human could manually track, and prioritize what matters.
Here’s what a SIEM actually does in practice:
Data Collection – Ingests logs from everywhere. Firewalls, servers, endpoints, cloud services, applications, databases, email gateways. Everything that generates a log, the SIEM swallows it.
Normalization – Raw logs from 50 different vendors all look different. The SIEM normalizes them into a common format so you can actually search and correlate across sources.
Correlation – This is the magic. A failed login from Russia isn’t alarming. A failed login from Russia followed by a successful login from the same IP followed by a new scheduled task? That’s an attack chain. SIEM connects the dots.
Alerting – When correlation rules trigger, the SIEM generates alerts ranked by severity. Good SIEMs use AI and machine learning to reduce false positives. Bad SIEMs drown you in noise.
Reporting – Compliance teams love SIEMs because they generate the audit trails and reports that regulations require.
Where SIEM Fits in the SOC vs VAPT Picture
Here’s the SOC vs VAPT vs SIEM relationship most articles never explain clearly:
SIEM is a tool. SOC is a team. VAPT is an activity.
You can’t compare them directly because they exist at different layers. But they depend on each other:
- SOC uses SIEM as its primary detection and investigation platform
- VAPT findings feed into SIEM as context for building better detection rules
- SIEM data validates VAPT by showing whether vulnerabilities are actually being exploited in the wild
Without SIEM, your SOC is blind. Without SOC, your SIEM is just an expensive log storage system nobody reads. Without VAPT, both your SOC and SIEM are defending against threats they don’t fully understand.
SOC vs VAPT vs SIEM: The Complete Comparison Table
Let’s cut through the confusion. Here’s the SOC vs VAPT vs SIEM breakdown in one table:
| Factor | SOC | VAPT | SIEM |
|---|---|---|---|
| What it is | Team + processes | Testing activity | Technology platform |
| Primary goal | Detect and respond to threats | Find vulnerabilities proactively | Collect, correlate, and alert on data |
| When it runs | 24/7/365 continuous | Periodic (quarterly/annually) | 24/7 continuous (automated) |
| Approach | Defensive (blue team) | Offensive (red team) | Supportive (data platform) |
| Output | Incident reports, threat containment | Vulnerability reports, risk ratings | Alerts, dashboards, compliance reports |
| Without it you’re | Blind to active attacks | Blind to unknown weaknesses | Drowning in uncorrelated logs |
| Typical cost | $150k-$500k+/year (in-house) | $10k-$100k per engagement | $20k-$200k+/year (platform) |
| Staffing needs | 5-15+ analysts (24/7 coverage) | 1-5 specialists per engagement | 1-3 engineers for management |
| MITRE ATT&CK alignment | Detection + Response | Simulates attack techniques | Provides data for both |
| ROI timeline | Months (ongoing value) | Immediate (per engagement) | Weeks to months (after tuning) |
My honest take: If you’re starting from zero and can only pick one investment, start with VAPT. Know your weaknesses first. Then build SOC capabilities (even basic ones). Then add SIEM to scale your detection. But ultimately, you need all three.
How SOC, VAPT, and SIEM Work Together: The Security Feedback Loop
This is the section that matters most in the entire SOC vs VAPT vs SIEM discussion. Because understanding each component in isolation is useless. The power is in how they feed each other.
The Feedback Loop Nobody Talks About
Here’s how a mature security program connects all three:
Step 1: VAPT Finds the Gaps
Your VAPT team runs a quarterly assessment. They find that your web application has an SQL injection vulnerability, your internal network has 14 machines with default credentials, and your cloud environment has 3 publicly exposed S3 buckets.
Step 2: Findings Feed Into SIEM Rules
Your SIEM engineer takes those VAPT findings and creates specific detection rules:
- Monitor for SQL injection patterns hitting the vulnerable endpoint
- Alert on authentication attempts using known default credential pairs
- Track access patterns to the exposed S3 buckets
Step 3: SOC Monitors for Exploitation
Now your SOC analysts have targeted detections. Instead of watching for “everything bad that could happen,” they’re watching for exploitation of known vulnerabilities in your specific environment.
Step 4: SOC Findings Feed Back Into VAPT Scope
When the SOC detects attack patterns or new threat intelligence relevant to your stack, that intelligence feeds into the next VAPT engagement’s scope. “We’ve seen increased scanning on port 8443. Make sure the next pentest hammers that service.”
Step 5: Repeat
This cycle creates compounding security improvement. Each iteration makes your SOC smarter, your VAPT more targeted, and your SIEM more precise.
Translation: Without this loop, you’re doing security in silos. And siloed security is how breaches happen. This is the core answer to the SOC vs VAPT question: they feed each other.
Real Numbers on Why This Matters
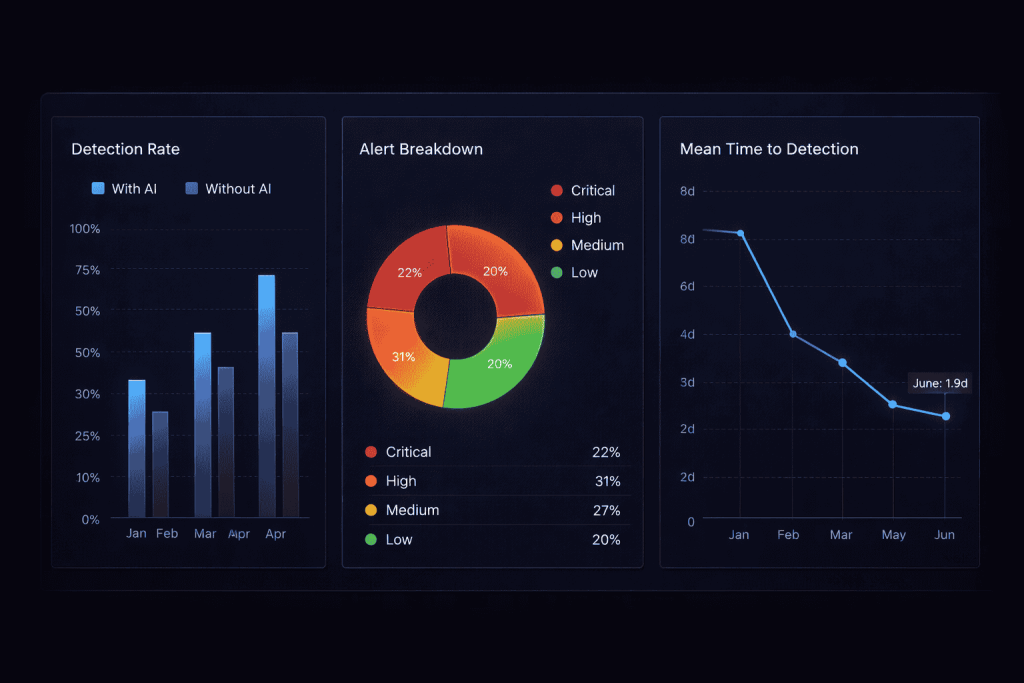
According to the ISC2 2025 Cybersecurity Workforce Study, there’s a global shortage of 4.8 million cybersecurity professionals. That means most SOC teams are understaffed and overwhelmed.
The average enterprise SOC deals with thousands of alerts per day. Most are false positives. Without VAPT findings to prioritize what matters, and without a properly tuned SIEM to reduce noise, your SOC analysts burn out chasing ghosts.
When VAPT findings directly inform SIEM correlation rules, false positive rates drop dramatically. Your SOC analysts spend less time on garbage alerts and more time on real threats.
That’s not efficiency for efficiency’s sake. That’s the difference between catching a breach in progress and reading about it in the news.
Building Your Security Program: Where to Start Based on Budget
Let’s be real about money. Not every organization has $500k to drop on a full SOC, annual VAPT engagements, and an enterprise SIEM platform.
Here’s the honest SOC vs VAPT vs SIEM priority order based on what you can actually afford:
Tier 1: Minimal Budget ($10k-$50k/year)
Start with VAPT.
Run at least one comprehensive VAPT engagement per year. Find your critical vulnerabilities. Fix them. This gives you the biggest immediate risk reduction per dollar spent.
For SIEM, start with open-source options like Wazuh or ELK Stack. They’re free, they work, and they’ll give you basic visibility.
For SOC, assign internal IT staff to review SIEM alerts during business hours. Not ideal, but better than nothing.
Tier 2: Growing Budget ($50k-$200k/year)
Add managed SOC capabilities.
You can’t build an in-house SOC at this budget, but you can outsource to a managed SOC / MDR provider. They’ll monitor your SIEM 24/7 and escalate real threats.
Increase VAPT frequency to quarterly. Include web applications, APIs, and cloud infrastructure.
Upgrade SIEM to a platform with better correlation and AI-powered alerting.
Tier 3: Mature Budget ($200k-$500k+/year)
Build the full loop.
In-house or hybrid SOC with dedicated L1, L2, and L3 analysts. Enterprise SIEM with SOAR integration for automated response. Quarterly VAPT plus continuous vulnerability scanning. Threat hunting program informed by VAPT findings and threat intelligence.
This is where the SOC vs VAPT debate stops being a comparison and becomes a collaboration. Your red team findings from VAPT directly improve your blue team detections in the SOC.
| Budget Tier | VAPT | SIEM | SOC | Security Maturity |
|---|---|---|---|---|
| $10k-$50k | Annual external VAPT | Open-source (Wazuh/ELK) | Part-time internal staff | Basic |
| $50k-$200k | Quarterly VAPT | Commercial or managed SIEM | Managed SOC/MDR | Intermediate |
| $200k-$500k+ | Quarterly VAPT + continuous scanning | Enterprise SIEM + SOAR | In-house/hybrid SOC 24/7 | Advanced |
XHack SOC: Where AI Closes the SOC vs VAPT Gap
Yeah, I’m about to pitch our own platform. But since I’m cursed with brutal honesty, here’s exactly what XHack SOC does for the SOC vs VAPT problem and where it doesn’t replace human judgment.
XHack SOC is an AI-powered Security Operations Center that we built because the traditional SOC model is broken for 90% of organizations. You either spend $500k+ on an in-house team, or you outsource to an MDR provider who treats your environment like one of 200 identical clients.
What XHack SOC Actually Delivers
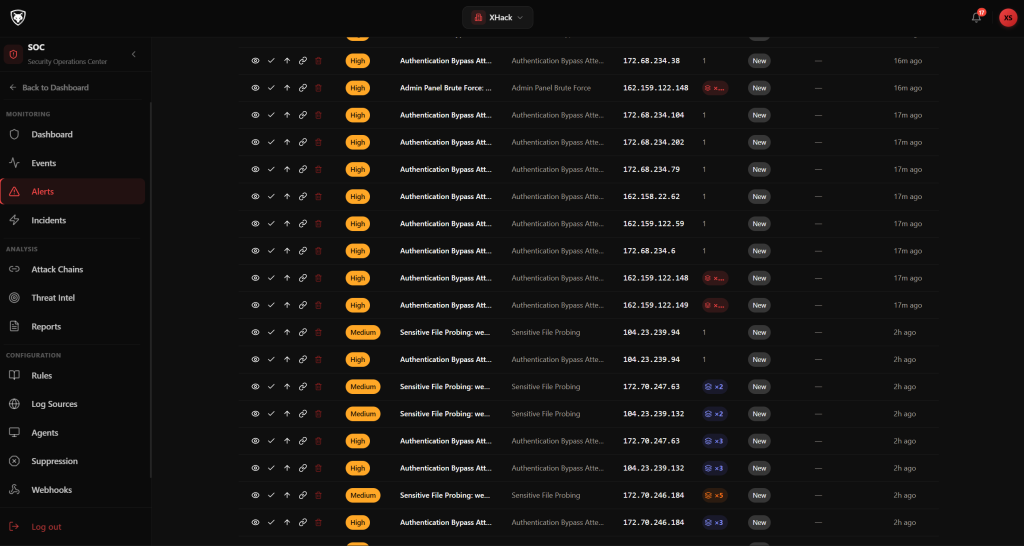
During live production testing, XHack SOC generated 10+ security alerts across multiple servers running against real environments and live websites. The system detected multiple attack patterns with near-zero false positives, automatically organizing everything into AI-powered attack chains.
Here’s how it bridges the SOC vs VAPT gap in practice:
Real-Time Threat Detection – Continuous monitoring across your infrastructure. No waiting for quarterly VAPT results to know you’re being attacked.
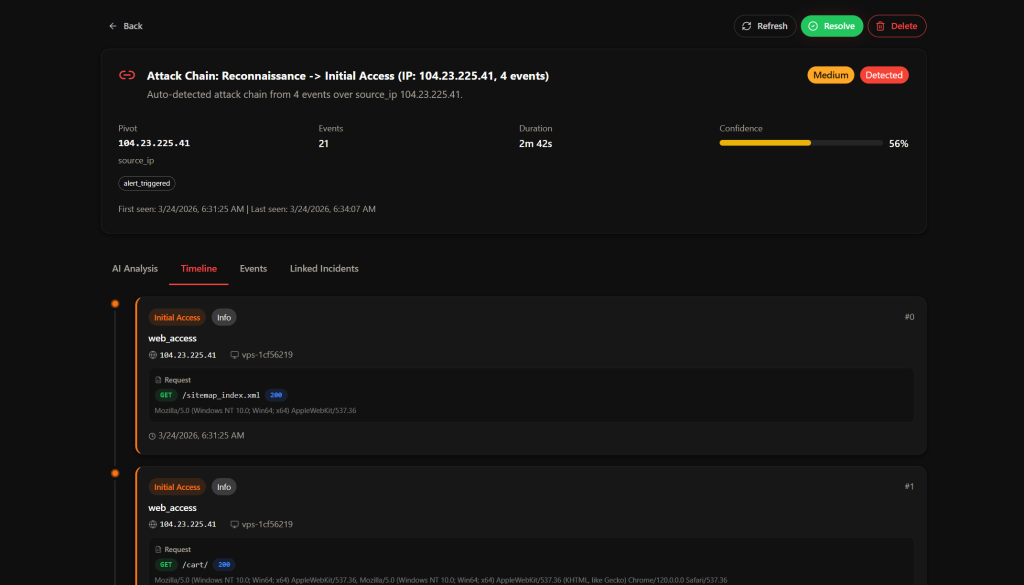
AI-Powered Attack Chain Reconstruction – When the SIEM catches individual events, XHack AI connects them into coherent attack narratives. Failed login + new process + outbound connection = complete attack chain, not three separate low-priority alerts.
VAPT-Informed Custom Detection Rules – This is the killer feature for the SOC vs VAPT integration. Take your VAPT findings, create custom detection rules using AI, and deploy targeted monitoring for your specific vulnerabilities.
Automated Alerting System – Alerts via email, n8n workflows, webhooks, or any integration you configure. No more SOC analysts staring at screens 24/7.
XHack AI Analysis – Intelligent security analysis and automated remediation guidance. The AI doesn’t just say “something bad happened.” It tells you what happened, maps it to MITRE ATT&CK techniques, and tells you how to fix it.
Centralized SOC Visibility – Single dashboard for all your log monitoring and threat data.
The SOC vs VAPT Workflow With XHack
Here’s how it works in practice:
- VAPT engagement finds SQL injection in your web app
- You create a custom rule in XHack SOC specifically monitoring for SQL injection patterns on that endpoint
- XHack AI monitors 24/7 and detects an actual exploitation attempt 3 weeks later
- Alert fires instantly via email and n8n with full context: source IP, attack pattern, MITRE ATT&CK mapping (T1190), and remediation steps
- Analyst reviews, takes action, reports. Total time: minutes, not hours.
Instead of manually monitoring logs all day, XHack AI analyzes activity, detects threats, organizes incidents, and provides remediation automatically.

What XHack SOC Won’t Do
- It won’t run your VAPT for you – You still need periodic offensive testing. XHack SOC is the defense layer, not the offense layer.
- It won’t replace human decision-making – AI removes the noise. Humans make the decisions. That’s by design.
- It won’t fix your architecture – If your network is flat, your passwords are “admin123”, and your S3 buckets are public, no SOC platform saves you. Fix the basics first.
But here’s what it changes for the SOC vs VAPT equation: You no longer need to choose between building an expensive SOC team or flying blind between VAPT engagements. XHack SOC gives you AI-powered continuous monitoring that makes your periodic VAPT findings actionable 24/7.
AI is not here to replace analysts. It’s here to remove the noise and let them focus on real threats. Security teams should not have to stare at screens all day anymore.
Common Mistakes in the SOC vs VAPT Decision
Mistake 1: Buying SIEM First, Then Wondering Why Nothing Works
This is the most expensive mistake in the SOC vs VAPT vs SIEM decision. Companies buy Splunk or Microsoft Sentinel, configure basic log ingestion, and then… nothing. Nobody watches the alerts. Nobody tunes the rules. Nobody investigates the findings.
A SIEM without a SOC is a Ferrari with no driver. Beautiful, expensive, going nowhere.
Mistake 2: Running VAPT Once and Never Again
“We did a pentest last year.” Congratulations. Your infrastructure has changed 500 times since then. New services deployed, old ones patched (or not), employees joined and left, cloud configs changed.
Annual VAPT is a minimum. Quarterly is better. Continuous vulnerability scanning between VAPT engagements is ideal.
Mistake 3: Building SOC Without VAPT Context
Your SOC is monitoring for threats, but what threats? Without VAPT findings to inform detection priorities, your SOC is guessing. The SOC vs VAPT relationship only works when offense informs defense. They’re building generic detection rules instead of targeted ones based on your actual attack surface.
The SOC vs VAPT answer isn’t either/or. It’s VAPT first to understand your weaknesses, then SOC to watch them continuously.
Mistake 4: Treating All Three as Separate Budget Lines
When finance asks “what’s the ROI on our SOC?” the answer should include VAPT findings it caught being exploited and SIEM data that proved the detection worked. They’re one security program, not three separate expenses.
Mistake 5: Ignoring AI-Powered Solutions
In 2026, the global SIEM market is projected to hit $13.55 billion by 2029, growing at 13.7% annually. AI-driven SOC capabilities are no longer optional. If your SOC analysts are manually correlating logs in 2026, you’re fighting a machine-speed adversary with human-speed defense.
Tools like XHack SOC exist specifically to bridge this gap with AI-powered detection, automated correlation, and intelligent alerting.
SOC vs VAPT vs SIEM: Quick Decision Framework
If you’re asking “which should I get first?” – here’s your answer:
If you don’t know your vulnerabilities: Start with VAPT. You can’t defend what you don’t understand.
If you know your vulnerabilities but can’t detect attacks: Add SIEM + SOC capabilities. Even basic monitoring is better than zero monitoring.
If you have all three but they don’t talk to each other: Fix the feedback loop. VAPT findings should directly inform SIEM rules, and SOC insights should shape VAPT scope.
If you want AI-powered detection without building a full SOC team: XHack SOC provides continuous monitoring, AI-driven attack chain detection, and automated alerting that bridges the gap between periodic VAPT and 24/7 defense.
If you’re an enterprise with budget: Build the full stack. In-house SOC, quarterly VAPT, enterprise SIEM with SOAR, and XHack AI for intelligent analysis on top. The SOC vs VAPT question disappears when both are running in sync.
FAQ: SOC vs VAPT Questions Answered
Is SOC vs VAPT really a comparison or are they complementary?
They’re absolutely complementary, not competitors. The SOC vs VAPT framing is misleading because they serve completely different functions. VAPT is periodic offensive testing that finds vulnerabilities before attackers do. SOC is continuous defensive monitoring that detects and responds to attacks in real time. A complete security program needs both. VAPT without SOC means you find holes but nobody watches them. SOC without VAPT means you’re defending blind.
Can a SIEM replace a SOC team?
No. A SIEM is a tool, not a team. Without trained analysts to investigate alerts, tune detection rules, and respond to incidents, a SIEM just generates alerts that nobody reads. However, AI-powered platforms like XHack SOC significantly reduce the human workload by automating correlation, alert triage, and remediation guidance. You still need human judgment for complex incidents, but AI handles the routine work that burns out L1 analysts.
How often should VAPT be conducted to keep SOC effective?
At minimum, run comprehensive VAPT quarterly. Between engagements, maintain continuous vulnerability scanning. Every VAPT report should generate specific SIEM detection rules that your SOC monitors. This creates the security feedback loop where each VAPT cycle makes your SOC smarter and each SOC finding makes your next VAPT engagement more targeted. Annual VAPT alone is no longer sufficient in 2026.
What’s the minimum viable security program for a startup?
Start with annual VAPT ($10k-$25k), deploy an open-source SIEM like Wazuh (free), and use an AI-powered SOC platform like XHack SOC for continuous monitoring. This gives you the SOC vs VAPT coverage at a fraction of enterprise costs. Total investment: under $30k/year for basic but functional security operations. That’s cheaper than one data breach notification.
How does XHack SOC handle the SOC vs VAPT integration?
XHack SOC allows you to create custom detection rules informed by your VAPT findings. When a VAPT engagement identifies a specific vulnerability, you build a targeted detection rule in XHack SOC using AI. The platform then monitors for exploitation attempts 24/7, generates AI-powered alerts with MITRE ATT&CK mapping, and provides automated remediation steps. This turns periodic VAPT findings into continuous defense without requiring a full in-house SOC team.
Conclusion
That’s a wrap on SOC vs VAPT vs SIEM and how to build a security program that doesn’t fall apart.
The SOC vs VAPT debate is a false choice created by vendors who want to sell you one thing. The reality is simple: VAPT finds the holes, SIEM provides the data, and SOC watches everything 24/7. Skip any one of them and you’ve got a gap that attackers will find.
If you want AI-powered SOC capabilities that turn your VAPT findings into 24/7 automated detection without hiring a 15-person security team, XHack SOC does exactly that. Not perfectly. Nothing is. But it’s the closest thing to having an always-on security analyst that doesn’t get alert fatigue, doesn’t miss correlations, and doesn’t need coffee breaks.
Security operations are evolving from manual monitoring to AI-driven defense. The organizations that understand SOC vs VAPT as a partnership instead of a competition will detect faster, respond smarter, and actually sleep at night.
Think I oversimplified something? Got a better SOC vs VAPT framework? Hit me up on LinkedIn. I respond to everything, including the people who think AI SOCs are overhyped.
