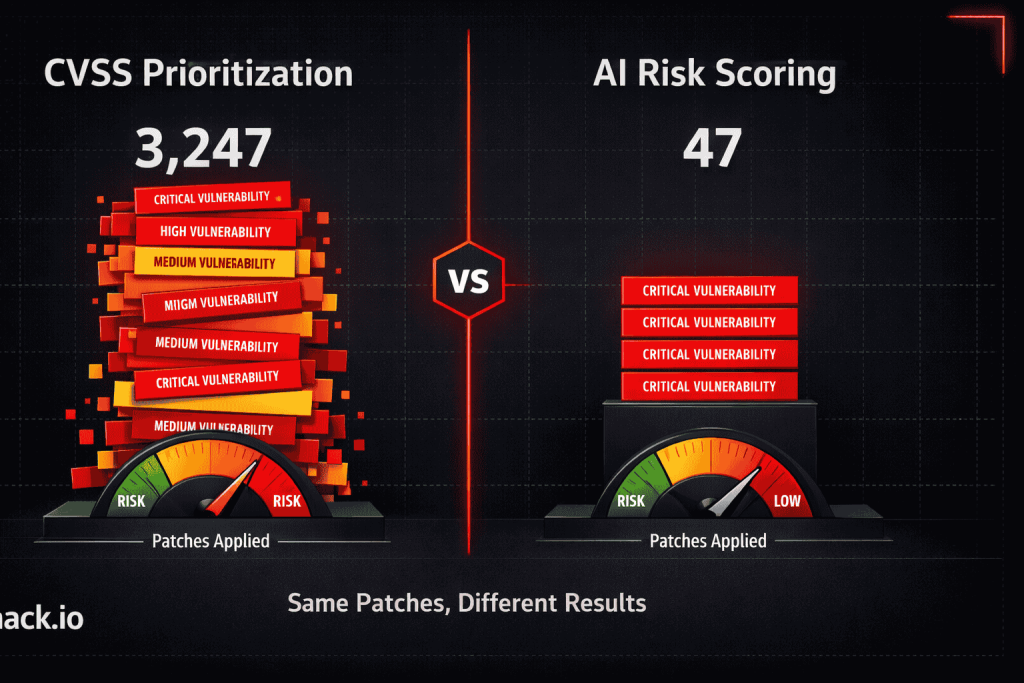
Read this in 30 seconds: Traditional vulnerability scanners dump 3,000 findings on your desk and call it security. AI vulnerability scanning tools actually tell you which 50 matter. They use predictive risk scoring, automated triage, exploit probability modeling, and contextual analysis to separate real threats from noise. Fewer than 5% of published CVEs ever get exploited in the wild, but legacy scanners treat every critical CVSS score like the building is on fire. This guide breaks down how AI vulnerability scanning actually works, what’s real vs marketing, and why your patching strategy is probably backwards.
Your vulnerability scanner found 3,247 findings last month. Your team patched 12.
That’s not a staffing problem. That’s a tool problem.
Every security team on the planet is drowning in vulnerability data. Over 35,000 CVEs were published in 2025, and 2026 is on pace to blow past that number. Traditional scanners find all of them. They flag everything with a CVSS score above 7.0 as “critical” and dump thousands of findings into a spreadsheet that nobody finishes reading.
And then everyone acts surprised when the breach comes through a medium-severity vulnerability that was actually being exploited in the wild while the team was busy patching a critical that no attacker has ever touched.
Here’s the thing. The problem was never finding vulnerabilities. Scanners have been good at that for 20 years. The problem is knowing which ones matter. And that’s exactly where AI vulnerability scanning changes everything.
Why Traditional Vulnerability Scanners Are Failing
Traditional vulnerability scanners do exactly one thing well: they find known vulnerabilities by matching signatures against a database. Nessus, Qualys, OpenVAS, they all work the same way. Scan the target, match CVEs, assign CVSS scores, generate a report.
The output is a giant list sorted by severity. Critical, High, Medium, Low, Informational. Your security team starts at the top and works down. Sounds logical.
It’s not.
CVSS scores measure theoretical severity. They don’t measure whether the vulnerability is actually being exploited. They don’t account for whether your specific instance is reachable from the internet. They don’t know if there’s a compensating control in front of it. They don’t care if the vulnerable component is running on a test server that gets rebuilt every morning.
A SQL injection on a public-facing API processing payment data and a SQL injection on an internal admin panel behind a VPN with parameterized queries get the same CVSS 9.8. Traditional scanners treat them identically. Your team spends the same time on both.
That’s why AI vulnerability scanning exists. Not to find more vulnerabilities. To find the ones that actually matter.
| Problem | Traditional Scanners | AI Vulnerability Scanning |
|---|---|---|
| Finding vulnerabilities | Good at it | Also good at it |
| False positive rate | 30-50% depending on scan type | Reduced by up to 90% |
| Prioritization | CVSS score only | Exploitability + context + threat intel |
| “Which ones matter?” | “All the criticals” | “These 50 specific ones, here’s why” |
| Patching guidance | “Apply vendor patch” | “Here’s the fix, here’s the risk if you don’t” |
| Continuous monitoring | Periodic scheduled scans | Real-time continuous assessment |
| Attack path awareness | Individual findings in isolation | Chained attack paths across assets |
What AI Vulnerability Scanning Actually Does (Not the Marketing Version)
Every vulnerability management vendor slapped “AI-powered” on their product page in 2025. Most of them just added a chatbot to the dashboard and called it artificial intelligence. Let’s be real about what AI vulnerability scanning actually means when it’s done properly.
Predictive Risk Scoring
This is the feature that matters most. Instead of relying on static CVSS scores, AI vulnerability scanning tools train models on historical exploitation data, threat intelligence feeds, dark web monitoring, and real-world attack patterns to predict which vulnerabilities are most likely to be exploited next.
CrowdStrike’s ExPRT.AI claims to pinpoint the 5% of vulnerabilities driving 95% of actual risk. Research consistently shows that fewer than 5% of published CVEs are ever exploited in the wild. Predictive scoring identifies that 5% so your team can ignore the 95% that attackers will never touch.
The models analyze factors that CVSS ignores completely:
- Does a public exploit exist for this CVE?
- Is the exploit being actively sold or discussed in underground forums?
- Is the vulnerable component exposed to the internet or buried behind multiple layers?
- Are threat actors targeting this specific vulnerability in current campaigns?
- What’s the EPSS (Exploit Prediction Scoring System) probability?
Translation: CVSS tells you how bad it could be. Predictive risk scoring tells you how bad it will be.
Automated Triage
Traditional workflow: scanner finds vulnerability, analyst investigates, analyst determines if it’s real, analyst determines severity in context, analyst writes a ticket, developer fixes it (eventually).
AI vulnerability scanning workflow: scanner finds vulnerability, AI validates exploitability, AI assesses context (is this internet-facing? is there a WAF in front? is the component actually in use?), AI prioritizes based on real risk, analyst reviews pre-triaged findings, developer gets a ticket with fix guidance already included.
The time savings are massive. What used to take an analyst 30 minutes per finding now takes 2 minutes of review. Multiply that across 3,000 findings per month and you’re recovering hundreds of analyst hours.
But here’s the catch. Automated triage is only as good as the context it has. If the AI doesn’t know your network topology, your business-critical assets, and your compensating controls, it’s just making educated guesses instead of dumb guesses. Better, but not perfect.
Attack Path Analysis
This is where AI vulnerability scanning gets genuinely impressive. Traditional scanners find individual vulnerabilities in isolation. AI-powered tools map how vulnerabilities chain together across your environment.
A medium-severity SSRF on a web application might seem low priority. But if that SSRF can reach an internal service with a high-severity RCE, which has access to a database containing customer PII, suddenly that “medium” is the first step in a critical attack chain.
Graph-based analysis maps these paths automatically. It shows you not just what’s vulnerable, but how an attacker would move through your environment chaining multiple findings together. That’s something a spreadsheet of CVSS scores will never tell you.
AI-Generated Remediation
Finding the vulnerability is half the problem. Knowing how to fix it is the other half, and it’s the half that actually reduces risk.
Modern AI vulnerability scanning tools don’t just say “apply vendor patch.” They generate context-specific remediation guidance:
- The exact code change needed for application vulnerabilities
- Configuration fixes for misconfigurations
- Compensating controls when patching isn’t immediately possible
- Priority ordering based on risk reduction per hour of effort
- Automated pull requests for known fixes in supported frameworks
GitHub’s Copilot Autofix resolved 460,258 security alerts in 2025, cutting mean remediation time nearly in half compared to manual fixes. That’s not a marginal improvement. That’s a fundamental shift in how fast organizations can actually reduce risk.
The AI Vulnerability Scanning Features That Are Real vs Marketing BS
Let’s separate what actually works from what’s just a sales pitch.
Actually Real and Useful
EPSS integration – The Exploit Prediction Scoring System uses machine learning to predict exploitation probability. It’s open, it’s data-driven, and it’s significantly better than CVSS at predicting which vulnerabilities attackers will actually use. Most serious AI vulnerability scanning tools integrate EPSS scores alongside or instead of raw CVSS.
Contextual false positive reduction – AI that understands application context can determine that a reported SQL injection isn’t actually exploitable because the application uses parameterized queries. This alone can reduce actionable findings by 80% without losing real positives.
Continuous scanning with change detection – AI vulnerability scanning tools that monitor for changes in your environment and trigger targeted scans when new assets appear, configurations change, or new CVEs are published. This replaces the quarterly scan cycle with always-on monitoring.
Exploit chain mapping – Graph-based analysis that shows how individual vulnerabilities combine into attack paths. This is genuinely useful for prioritization and for communicating risk to leadership.
Mostly Marketing Hype
“AI-powered scanning engine” – Most vendors claiming this just added ML-based crawling improvements to their existing scanner. The scan itself isn’t fundamentally different. They find the same vulnerabilities. The AI part is in what happens after the scan, not during it.
“Zero false positives” – Nobody has zero false positives. Anyone claiming this is lying. The best AI vulnerability scanning tools reduce false positives dramatically, but eliminating them entirely isn’t possible without proof-based validation on every single finding.
“Replace your security team” – No. AI vulnerability scanning removes the noise so your security team can focus on real threats. It doesn’t replace human judgment for complex decisions, business context, or risk acceptance.
Impact on Patching: Why Your Remediation Strategy Needs to Change
Here’s where AI vulnerability scanning creates the biggest real-world impact. Not in finding more bugs, but in fixing the right ones faster.
The Old Way (Still How Most Organizations Operate)
- Run quarterly vulnerability scan
- Get 5,000 findings
- Sort by CVSS severity
- Start patching criticals
- Run out of time/resources at finding #200
- Repeat next quarter
- Get breached through finding #3,847 that was actually being exploited
The AI-Powered Way
- Run continuous AI vulnerability scanning
- AI filters to 200 findings that represent actual risk
- AI prioritizes by exploit probability + business context + attack path
- Top 30 findings get patched immediately (highest risk reduction per effort)
- AI generates remediation code or configuration fixes
- Developers get contextual fix guidance in their existing workflow
- AI verifies the fix worked and removes the finding
- Continuous monitoring catches new risks as they emerge
The difference isn’t just speed. It’s focus. When your team patches 30 findings that are actually being exploited instead of 200 findings that theoretically could be exploited, risk drops faster with less effort.
Metrics That Actually Matter
If your vulnerability management program still measures success by “number of criticals patched,” you’re measuring the wrong thing. AI vulnerability scanning enables better metrics:
| Old Metric | Why It’s Wrong | Better Metric |
|---|---|---|
| Total criticals patched | Not all criticals are equal | Exploitable findings remediated |
| Mean time to patch (all findings) | Includes noise alongside real threats | Mean time to remediate actively exploited CVEs |
| Scan coverage percentage | Scanning isn’t the bottleneck | Reduction in exploitable attack paths |
| Number of findings closed | Closing informational findings isn’t risk reduction | Risk score reduction over time |
XHack SOC: Where AI Vulnerability Scanning Meets Continuous Detection
So yeah, I’m going to mention our own platform. One section. Here’s what XHack SOC does for the AI vulnerability scanning workflow and where it fits.
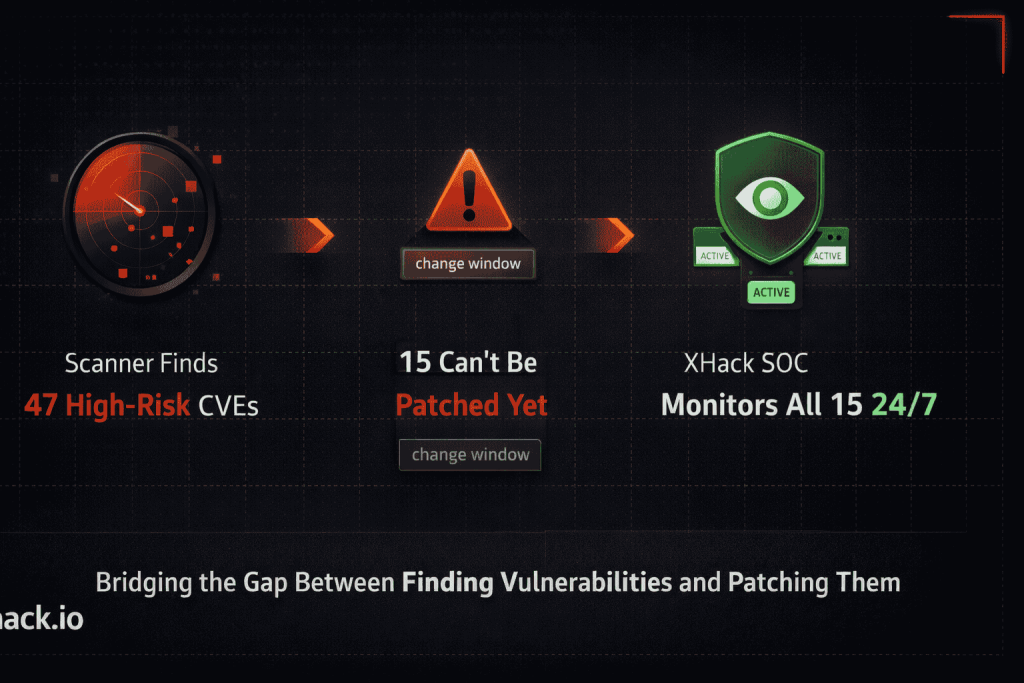
Most AI vulnerability scanning tools find the problems. XHack SOC watches for exploitation of those problems in real time.
Here’s the actual workflow:
Your AI vulnerability scanning tool identifies 47 high-risk findings across your infrastructure. 15 of them can’t be patched immediately because of change windows, dependencies, or business constraints. Those 15 are now known, unpatched, exploitable vulnerabilities.
XHack SOC takes those 15 findings and creates targeted detection rules for each one. If someone tries to exploit that unpatched SSRF while you’re waiting for the maintenance window, XHack AI detects the attempt, maps it to the specific CVE and MITRE ATT&CK technique, generates an alert with remediation context, and sends it to your team instantly via email, n8n, or whatever integration you’ve configured.
The AI doesn’t just detect the exploit attempt. It reconstructs the attack chain, showing whether the attacker got further than the initial vulnerability. Did they chain it into lateral movement? Did they access sensitive data? The full picture, automatically.
That’s the gap between “we know about the vulnerability” and “we’ll catch anyone trying to exploit it.” AI vulnerability scanning finds the holes. XHack SOC watches them until they’re fixed.
FAQ: AI Vulnerability Scanning Questions Answered
Does AI vulnerability scanning replace traditional scanners like Nessus or Qualys?
Not entirely. AI vulnerability scanning builds on top of traditional scanning, not instead of it. You still need a scanner to discover vulnerabilities by matching against CVE databases. The AI layer adds predictive risk scoring, contextual analysis, false positive reduction, and remediation prioritization. Think of traditional scanners as the eyes and AI vulnerability scanning as the brain that makes sense of what the eyes see.
How accurate is predictive risk scoring compared to CVSS?
EPSS-based predictive scoring has been shown to be significantly more accurate at predicting actual exploitation than CVSS alone. Research consistently finds that fewer than 5% of CVEs get exploited in the wild, but traditional CVSS prioritization doesn’t identify which 5%. AI vulnerability scanning models trained on exploit databases, threat intelligence, and historical patterns can predict exploitation probability with much higher accuracy, letting teams focus patching on the vulnerabilities attackers will actually target.
What’s the minimum infrastructure needed to benefit from AI vulnerability scanning?
You don’t need an enterprise budget to start. Open-source scanners like OpenVAS provide the detection layer for free. Add EPSS scores (publicly available) for better prioritization. Use AI-powered triage tools to filter findings. Even without a commercial AI vulnerability scanning platform, combining these free resources dramatically improves prioritization over raw CVSS sorting. As your program matures, commercial platforms add continuous monitoring, attack path analysis, and automated remediation.
How does AI vulnerability scanning handle zero-day vulnerabilities?
Zero-days by definition aren’t in CVE databases yet, so no scanner, AI or not, will flag them through signature matching. However, AI vulnerability scanning tools that include behavioral analysis and anomaly detection can identify suspicious patterns that might indicate zero-day exploitation. When a new CVE is published, AI-powered tools can rapidly assess which of your assets are affected and predict exploitation likelihood based on the vulnerability’s characteristics, before public exploit code even exists.
Conclusion
AI vulnerability scanning isn’t about finding more vulnerabilities. It’s about finding the ones that matter.
Your scanner already finds everything. The problem was never discovery. The problem was drowning in 3,000 findings and guessing which 30 to fix first. AI vulnerability scanning removes the guessing with predictive risk scoring, contextual analysis, and exploit probability modeling.
The organizations that adopted AI vulnerability scanning in 2025 patched fewer total vulnerabilities but reduced actual risk faster than teams patching by CVSS score. Less work, better results. That’s the entire pitch.
Stop patching by severity score. Start patching by exploit probability. And monitor the gaps with continuous detection while you wait for the maintenance window.
The scanners found the holes 20 years ago. AI finally tells you which ones the attackers are walking through.
Follow Us on LinkedIn: @xhack
