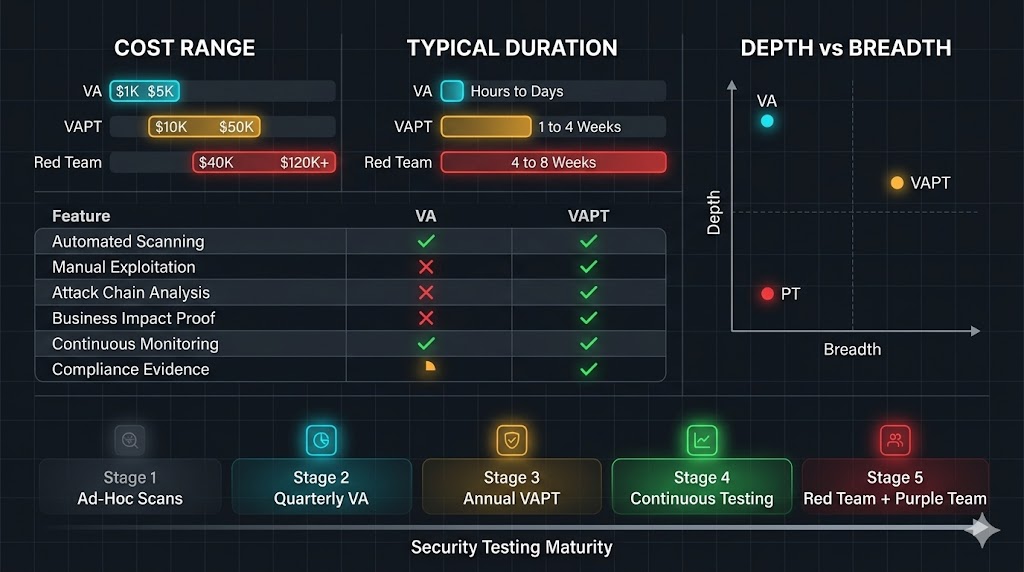
30-Second Summary: Vulnerability Assessment vs Penetration Testing, A standalone vulnerability assessment (VA) costs $1,000 to $5,000 and finds known weaknesses across your environment using automated scanners. A full VAPT engagement adds manual penetration testing on top of that, costing $5,000 to $50,000 or more, but proves which vulnerabilities are actually exploitable and what the business impact looks like. PCI DSS 4.0 (fully enforced since March 2025) requires both quarterly vulnerability scans and annual penetration tests. SOC 2, ISO 27001, and HIPAA all carry their own testing mandates.
The right choice depends on your maturity level, compliance requirements, budget, and whether you need a list of what’s broken or proof of what an attacker can actually do with it. This guide breaks down exactly when each option makes sense and when you’re wasting money by choosing the wrong one.
Here’s a question that burns more cybersecurity budgets than it should: do you need a vulnerability assessment, or do you need a full VAPT?
The answer matters more than most organizations realize. Pick the wrong one and you either overspend for depth you don’t need yet, or you underspend and hand your auditor a report that proves nothing about real-world risk. Both mistakes are expensive. One just takes longer to catch up with you.
The confusion starts with the terminology itself. Vendors use VA, PT, and VAPT interchangeably on their sales pages because blurring the lines makes it easier to upsell. Compliance frameworks reference both but rarely explain the distinction clearly enough for a non-technical decision maker to act on it. And internally, security teams sometimes run automated scans and call them penetration tests, which creates a false sense of assurance that evaporates the moment a real attacker shows up.
This article is the practical guide. No vendor pitches. No acronym soup without context. Just a clear breakdown of what each service actually delivers, what it costs, what compliance frameworks require, and how to decide which one fits your organization right now.
What a Vulnerability Assessment Actually Is
A vulnerability assessment is a broad, largely automated process designed to identify known security weaknesses across your systems, applications, and network infrastructure. Think of it as a diagnostic scan. It tells you what’s potentially broken, but it doesn’t try to break anything.
The process works like this. Automated scanning tools like Nessus, Qualys, or OpenVAS run against your target environment. They check system configurations, software versions, and exposed services against massive databases of known vulnerabilities (CVEs). The output is a report listing every identified weakness, typically ranked by severity using the Common Vulnerability Scoring System (CVSS).
A credentialed VA scan (where the scanner authenticates to each host) produces significantly more accurate results than an unauthenticated scan. It can see patch levels, local configurations, and internal services that external-only scanning misses entirely. If your VA vendor isn’t performing credentialed scans, you’re getting a surface-level view at best.
What you get from a vulnerability assessment:
A comprehensive list of known vulnerabilities across your scanned environment. CVSS severity rankings for prioritization. Configuration weaknesses and missing patches. A baseline snapshot of your security posture at a specific point in time. Remediation recommendations tied to each finding.
What you don’t get:
Proof that any of those vulnerabilities are actually exploitable in your specific environment. Understanding of how an attacker could chain multiple low-severity findings into a critical compromise. Business impact analysis showing what data or systems could actually be reached. Testing of business logic flaws, complex attack paths, or human-factor vulnerabilities.
A vulnerability assessment is identification without exploitation. It tells you the lock is old. It doesn’t tell you whether someone can actually pick it.
Typical cost: $1,000 to $5,000 per assessment, depending on scope and whether it’s automated-only or includes manual validation.
Typical duration: Hours to a few days for automated scanning. One to two weeks if manual validation and reporting are included.
Recommended frequency: Monthly or quarterly at minimum. Many mature organizations run continuous scanning as part of their vulnerability management program.
XHack VA Scan: Run Your Own Vulnerability Assessment, Securely
Most vulnerability assessment tools fall into one of two categories. Enterprise platforms that cost a fortune and take weeks to deploy. Or free scanners that dump raw output nobody can act on. Neither option works if you want to run a proper VA without handing your entire asset inventory to a third party and hoping for the best.
That’s the problem XHack’s VA Scan platform was built to solve.
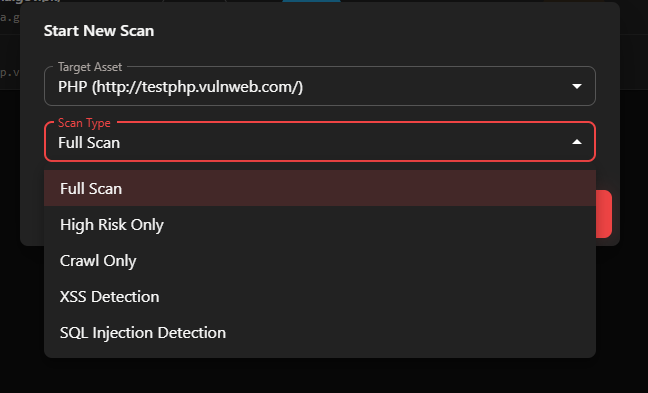
XHack VA Scan is a secure web application that lets you run full vulnerability assessments against your own assets, on your terms, with complete control over your data. No agents to install on production systems. No permanent data retention you can’t control. No black-box vendor access to your infrastructure details.
Here’s how it actually works.
Asset verification and scoping. You register and verify the assets you want scanned. The platform confirms ownership before any scanning begins, which prevents unauthorized testing and keeps everything within your approved scope. This is the step most self-service scanning tools skip entirely, and it’s the step that separates a legitimate VA from someone randomly firing Nmap at things they don’t own.

Multi-mode scanning. XHack VA supports multiple scan types depending on what you need to assess. Whether you’re testing a web application, an external network perimeter, or specific infrastructure components, the platform configures the scan engine to match your target. You’re not locked into a single scan profile that tries to be everything at once.
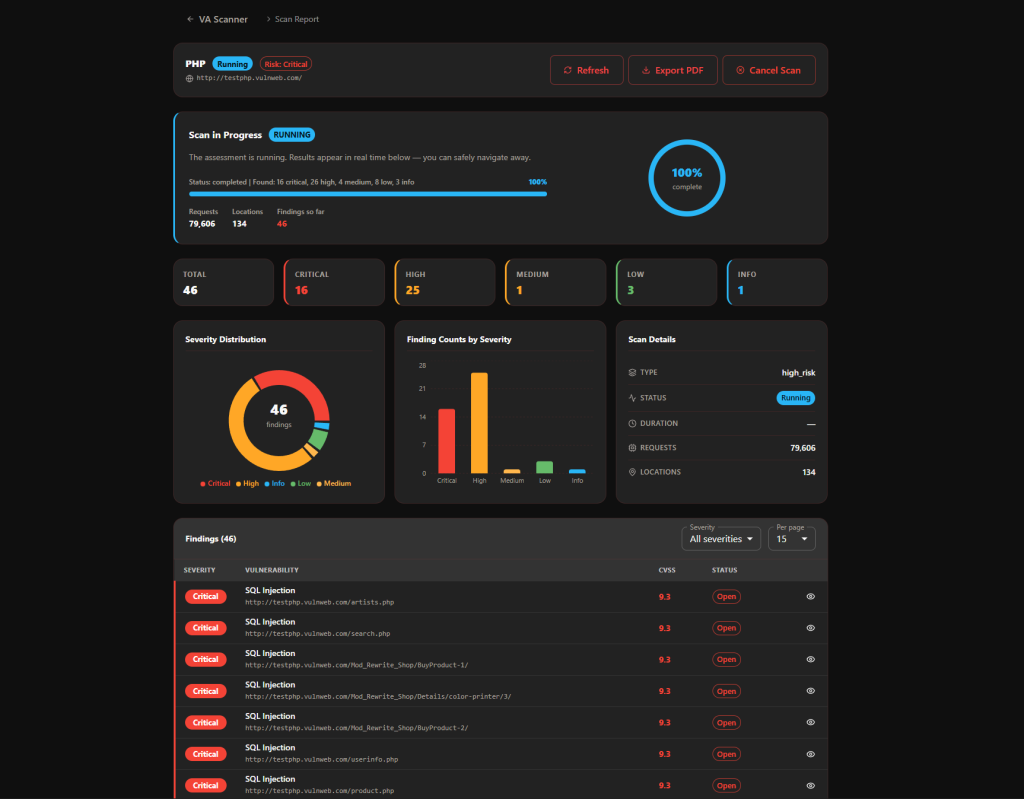
Real-time monitoring. You don’t submit a scan and wait three days for an email with a PDF attached. The platform shows scan progress in real time, so you can see what’s being tested, what’s been found so far, and how far along the assessment is. You can even generate interim reports while a scan is still running if you need preliminary findings before the full assessment completes.
Role-specific reporting. This is where it gets genuinely useful. XHack VA doesn’t just produce a single vulnerability dump. It generates different report formats tailored to different audiences. A CISO report that focuses on risk posture, business impact, and executive summary metrics. A developer report that provides technical remediation details, affected components, and fix guidance. A compliance report structured for audit evidence. Same scan data, different lenses depending on who needs to act on the findings.
A dashboard that actually helps. The central dashboard gives you a consolidated view of all your scanned assets, vulnerability trends over time, severity breakdowns, and remediation status. You can filter by vulnerability type, severity level, asset group, or scan date. It’s designed so that security teams, developers, and stakeholders can all find what they need without wading through a 200-page PDF.
Full data control. Every piece of data generated by your scans belongs to you. You can access it, export it, and delete it whenever you want. The platform doesn’t retain your scan results indefinitely or use your data for anything beyond delivering your reports. If you want everything wiped after you’ve downloaded your findings, you wipe it. That level of control matters when you’re scanning environments that contain sensitive systems or regulated data.
XHack VA Scan is built for development teams running security checks before deployment, security teams managing ongoing vulnerability hygiene across multiple assets, and stakeholders who need clean reporting without waiting weeks for a consulting engagement to deliver results.
What Penetration Testing Actually Is
Penetration testing is a targeted, manual, human-driven process where skilled security professionals simulate real-world attacks against your environment. The goal isn’t just to find vulnerabilities. It’s to exploit them, chain them together, and demonstrate exactly what an attacker could achieve.
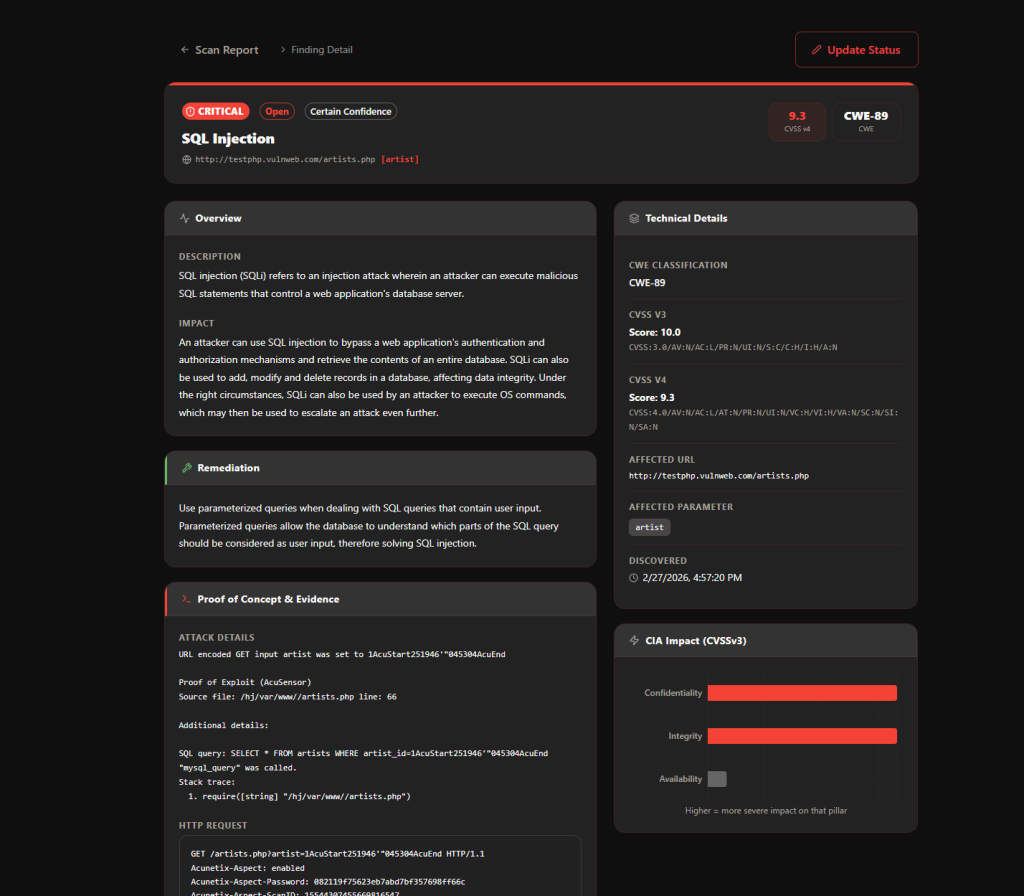
A penetration tester doesn’t just flag that your web application has a potential SQL injection point. They exploit it, extract data, escalate privileges, and document the full attack path from initial access to business impact. They think creatively, test business logic, and find vulnerabilities that automated scanners structurally cannot detect.
The methodology follows established frameworks like OWASP Testing Guide, PTES, or NIST SP 800-115 and typically includes these phases: reconnaissance and information gathering, vulnerability identification, exploitation, post-exploitation and lateral movement, and detailed reporting with proof-of-concept evidence.
Penetration tests come in several flavors depending on the tester’s starting knowledge. Black box testing gives the tester no prior information, simulating an external attacker. White box testing provides full access to source code, architecture documents, and credentials, enabling the deepest possible analysis. Gray box testing falls between the two, typically providing authenticated access but limited internal documentation.
What you get from a penetration test:
Validated, exploitable vulnerabilities with proof-of-concept demonstrations. Attack chain analysis showing how multiple findings combine for maximum impact. Business impact assessment tied to specific data, systems, or processes. Detailed remediation priorities based on real exploitability, not just CVSS scores. Evidence that satisfies compliance auditors and demonstrates due diligence.
What you don’t get:
Broad coverage of every system in your environment (penetration tests are targeted by scope). Continuous monitoring or ongoing vulnerability tracking. A substitute for regular vulnerability scanning.
Typical cost: $5,000 to $50,000 for most engagements. Enterprise-grade or continuous testing platforms run $75,000 to $150,000 or more annually. Web application pentests average around $12,500. External network tests average around $10,000. Internal network tests run $7,500 to $30,000. Be cautious of any “penetration test” priced under $4,000. At that price point, you’re almost certainly receiving an automated vulnerability scan marketed as a pentest.
Typical duration: One to four weeks depending on scope and complexity.
Recommended frequency: At least annually. After any significant infrastructure or application changes. More frequently for high-risk or rapidly changing environments.
VAPT: When You Combine Both
VAPT (Vulnerability Assessment and Penetration Testing) isn’t a separate service. It’s the combination of both approaches into a single engagement. You start wide with vulnerability scanning to identify the full landscape of potential weaknesses, then go deep with penetration testing on the high-risk findings to validate real-world exploitability.
This is the approach that the most mature security organizations use because it solves the weaknesses of each individual method. Vulnerability assessments alone leave you blind to actual impact. Penetration tests alone waste expensive manual testing hours on issues that a simple patch could have resolved.
The typical VAPT workflow looks like this. Run credentialed vulnerability scans across the full target environment. Prioritize findings by CVSS severity, focusing on anything rated 7.0 or higher. Conduct manual penetration testing on critical systems, high-value targets, and findings that need exploitation to validate. Document everything: the full vulnerability inventory, the exploitation results, the business impact analysis, and prioritized remediation steps. Retest after remediation to confirm fixes are effective.
Typical cost: $10,000 to $60,000 or more, depending on scope. Higher than either service alone, but more cost-effective than running them as completely separate engagements.
The Compliance Factor: What Frameworks Actually Require
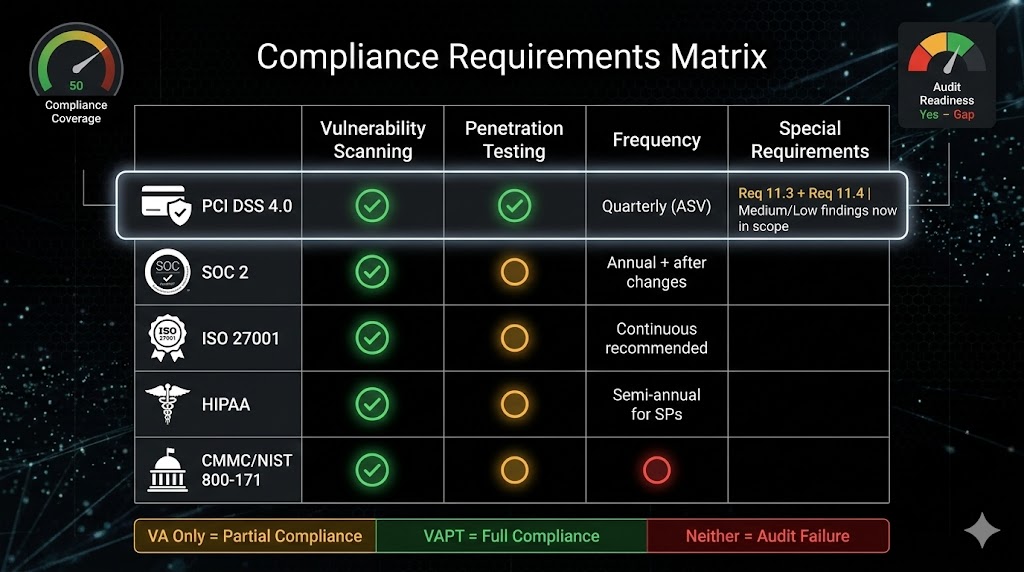
Compliance is often what forces the VA vs VAPT decision. Here’s what the major frameworks actually mandate, because “we need to be compliant” is not specific enough to build a testing program on.
PCI DSS 4.0 (fully enforced since March 31, 2025). This is the most prescriptive framework on testing requirements. Requirement 11.3 mandates quarterly internal and external vulnerability scans. External scans must be performed by a PCI SSC Approved Scanning Vendor (ASV). Requirement 11.4 mandates annual penetration testing (both internal and external) and after any significant changes to the cardholder data environment. Application-layer and network-layer testing are both required. Segmentation testing is required annually, or every six months for service providers. PCI DSS 4.0 also now requires remediation of medium and low findings (not just critical and high) based on risk analysis, and multi-tenant service providers must support customer penetration testing.
SOC 2. While SOC 2 doesn’t explicitly mandate penetration testing by name, the Trust Services Criteria (specifically CC4.1 and CC7.1) require organizations to evaluate the effectiveness of security controls. A penetration test provides the strongest evidence that controls are working as intended. In practice, most SOC 2 auditors expect to see both vulnerability scanning and penetration testing as part of the evidence package.
ISO 27001. Requires processes for identifying and addressing security vulnerabilities as part of the Information Security Management System (ISMS). Annual penetration testing is the industry standard for demonstrating compliance with Annex A controls related to technical vulnerability management.
HIPAA. The Security Rule’s Evaluation standard (164.308(a)(8)) requires periodic technical and non-technical evaluations. Quarterly vulnerability scanning is strongly recommended. Annual penetration testing is the accepted industry standard for meeting this requirement, though the regulation doesn’t specify exact methodologies.
CMMC / NIST 800-171. Includes specific controls requiring security testing and vulnerability exploitation validation. Penetration testing provides the evidence that these controls are implemented and effective.
The pattern across all major frameworks is consistent: vulnerability scanning provides the baseline hygiene, and penetration testing provides the validation. If you’re subject to any of these standards, you need both.
The Decision Framework: When to Choose VA Only
A standalone vulnerability assessment is the right choice when your organization meets most of these conditions.
You’ve never had a formal security assessment. If you’re starting from zero, running a comprehensive VA first makes sense. There’s no point paying for manual exploitation when you likely have hundreds of unpatched systems and misconfigurations that automated scanning will catch immediately. Fix the basics first.
Your budget is under $5,000. A quality VA is achievable in this range. A quality pentest is not. Don’t buy a cheap “pentest” that’s actually just an automated scan with a different label. You’re better off acknowledging you’re getting a VA and spending the money on a good one with credentialed scanning and manual validation.
You need continuous baseline monitoring. Vulnerability scanning integrates into CI/CD pipelines, runs weekly or monthly, and provides ongoing visibility into your patch management effectiveness. Penetration tests are point-in-time engagements. For continuous posture management, VA is the operational tool.
Your compliance requirements only mandate scanning. Some PCI DSS SAQ types and certain regulatory contexts only require quarterly vulnerability scans. If that’s genuinely all your compliance framework demands (verify this carefully), a VA meets the requirement.
You’re preparing for a pentest. Running a VA before a penetration test is a smart use of resources. It lets you remediate the low-hanging fruit so your pentest hours are spent on the complex findings that actually require human expertise to validate.
The Decision Framework: When to Choose Full VAPT
A full VAPT engagement is the right choice when your organization meets most of these conditions.
You process or store sensitive data. If you handle payment card data, protected health information, personally identifiable information, or intellectual property, you need to know what an attacker can actually do, not just what’s theoretically vulnerable. The business impact of a breach in these environments justifies the investment in exploitation-based testing.
Compliance requires penetration testing. PCI DSS 4.0 Requirement 11.4, SOC 2 evidence expectations, ISO 27001 Annex A, HIPAA Security Rule evaluations, and CMMC all require or strongly expect penetration testing. A VA alone won’t satisfy these requirements regardless of how comprehensive it is.
You’ve been doing VAs but findings keep recurring. If your vulnerability scan reports show the same findings quarter after quarter, you have a remediation problem that scanning alone can’t solve. A penetration test that demonstrates real exploitation and business impact is often what it takes to get remediation prioritized and funded by leadership.
You need to validate specific controls. Network segmentation, access controls, identity management, application security, and incident detection all require testing under real attack conditions to prove they work. VAs check configuration. Pentests check effectiveness.
A major change just happened. New application deployment, cloud migration, merger or acquisition, significant infrastructure change. Any of these events warrant a VAPT engagement to validate that the new environment is secure, not just configured correctly.
Your customers or partners require it. Enterprise procurement processes increasingly require evidence of penetration testing as part of vendor risk assessments. A vulnerability scan report won’t satisfy a customer security questionnaire asking for pentest results.
You want to understand real risk, not just theoretical risk. CVSS scores tell you theoretical severity. A penetration test tells you that a CVSS 5.0 finding in your environment actually chains with two other findings to enable full domain compromise. That’s the difference between a spreadsheet and an actual risk assessment.
The Cost of Choosing Wrong
Choosing a VA when you need a VAPT creates a specific failure mode: you have a long list of findings ranked by CVSS scores, your leadership thinks security has been “tested,” and nobody knows which of those findings actually expose the business to compromise. When an attacker arrives, they don’t care about your CVSS rankings. They care about what’s exploitable.
Choosing a VAPT when you need a VA (or aren’t ready for one) also wastes money. If your environment has 500 unpatched critical vulnerabilities, a penetration tester will find them in the first hour and spend the rest of the engagement exploiting obvious weaknesses that a $2,000 scan would have caught. You’ll get a report full of findings that all boil down to “patch your systems,” which you could have learned for a fraction of the cost.
The Verizon 2025 DBIR confirmed that vulnerability exploitation remains a top initial access vector for breaches. The average cost of a data breach in 2025 hit $4.88 million globally according to IBM. A quality VAPT engagement at $15,000 to $30,000 represents less than 1% of that average breach cost. A VA at $2,000 to $5,000 represents a rounding error.
The question isn’t whether you can afford testing. The question is whether you’re buying the right test for your current situation.
Building a Mature Testing Program: The Practical Roadmap (Vulnerability Assessment vs Penetration Testing)
The organizations that get this right don’t treat VA and VAPT as competing options. They build a program that uses both at appropriate frequencies based on risk.
Phase 1: Establish baseline (Months 1 to 3). Deploy credentialed vulnerability scanning across all systems. Run monthly or quarterly. Establish a vulnerability management process with SLAs for remediation by severity. Fix the critical and high findings first.
Phase 2: First penetration test (Months 3 to 6). Once scan results are manageable, engage a qualified penetration testing firm for a scoped VAPT. Focus on your highest-value assets: production applications, customer-facing systems, and anything touching sensitive data. Use the pentest results to validate that your remediation efforts are actually reducing real risk, not just clearing scan findings.
Phase 3: Continuous improvement (Ongoing). Run vulnerability scans continuously or at least monthly. Conduct annual penetration tests at minimum. Test after every significant change. Feed pentest findings back into your vulnerability management process. Track metrics: mean time to remediate, percentage of findings recurring between tests, and exploitable findings per test.
Phase 4: Advanced testing (Year 2 and beyond). Add red team exercises to test detection and response capabilities. Introduce purple team sessions where attackers and defenders collaborate. Consider continuous penetration testing platforms for rapidly changing environments. Expand scope to include social engineering, physical security, and cloud-specific testing.
This is how you move from “checking boxes” to actually understanding and reducing your risk.
Frequently Asked Questions
How often should I run a VA vs a full penetration test?
Run vulnerability scans monthly at minimum, or continuously if your environment supports it. PCI DSS 4.0 mandates quarterly external scans by an ASV and quarterly internal scans. Penetration tests should be conducted at least annually and after any significant infrastructure or application changes. Organizations with high-risk environments or rapid change cycles benefit from semi-annual or quarterly penetration testing. The key principle is that scanning is your ongoing diagnostic and penetration testing is your periodic deep validation.
Can a vulnerability scan fail a compliance audit if I don’t also have a penetration test?
Yes, for most major frameworks. PCI DSS 4.0 explicitly requires both quarterly vulnerability scans (Requirement 11.3) and annual penetration tests (Requirement 11.4). Presenting only scan results when a pentest is required will result in a compliance gap. SOC 2, ISO 27001, and HIPAA all expect penetration testing evidence as part of control effectiveness validation. Auditors distinguish between identification (scanning) and validation (testing). You need both to demonstrate due diligence.
What certifications should I look for in a penetration testing provider?
Look for testers holding OSCP (Offensive Security Certified Professional), OSCE, OSWE, CREST certification, or GPEN/GXPN from SANS. For PCI-specific testing, the firm should understand PCI DSS Requirement 11.4 methodology requirements in detail, though they don’t need to be a QSA or ASV. Ask about methodology (OWASP, PTES, NIST SP 800-115), request sample reports, and verify that testing includes manual exploitation, not just automated scanning. Experienced testers with relevant certifications typically charge $250 to $500 per hour, but deliver significantly more thorough and reliable results than junior testers at lower rates.
Need a vulnerability assessment or full VAPT engagement that actually tells you something useful? The XHack team delivers both, scoped to your environment, your compliance requirements, and your actual risk profile. No automated-scan-disguised-as-a-pentest. No generic reports. Just clear findings, real exploitation evidence, and remediation guidance that your engineering team can act on.
Follow Us on XHack LinkedIn and XHack Twitter
