Read this in 30 seconds: MITRE ATT&CK is a free framework with 14 tactics and 203+ techniques built from real-world attacks. Most pentests find vulnerabilities but ATT&CK-based pentests test whether your SOC would even notice an attacker inside your network. Map every pentest action to an ATT&CK technique ID so your blue team knows exactly what to detect. In a real engagement, 78% of tested techniques went completely undetected by a company that thought their security was solid. Modern attackers focus on staying hidden, not causing immediate damage. AI-powered SOC tools like XHack SOC can map detections to ATT&CK automatically, removing the manual correlation nightmare and letting analysts focus on real threats instead of drowning in alerts.
Most pentesters treat MITRE ATT&CK like a poster on their wall. They know it exists. They might reference it in a report. But they never actually use it to plan an attack or build a defense.
And that’s why most penetration tests are glorified vulnerability scans with extra steps.
Here’s what nobody in the cybersecurity conference circuit wants to admit: the gap between “knowing about ATT&CK” and “operationalizing ATT&CK” is where 90% of security teams fall flat on their face. They’ll map a finding to T1190 in their report, pat themselves on the back, and call it a day.
Meanwhile, real attackers are chaining 8 techniques together across 5 tactics – and your SOC is drowning in 10,000 alerts trying to catch them.
Nobody’s doing the homework. So I did.
I spent weeks mapping real-world pentesting engagements to the MITRE ATT&CK framework, testing how it actually works for both offense and defense. This guide shows you how to use ATT&CK the way it was meant to be used – not as a checkbox, but as a battle plan.
MITRE ATT&CK in Penetration
What Is the MITRE ATT&CK Framework? – Skip the Wikipedia Version

MITRE ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. That’s the boring textbook answer.
Here’s what it actually is: a cheat sheet built from real attacks.
MITRE Corporation started building this thing back in 2013 by studying how attackers actually moved through networks after getting initial access. Not theoretical attacks. Not “what could happen.” What did happen, documented from real incidents.
Fast forward to 2026, and the Enterprise matrix alone has 14 tactics, 203+ techniques, and 453+ sub-techniques. It covers Windows, Linux, macOS, cloud environments, mobile, and even ICS (industrial control systems).
But here’s the thing.
Most people look at the ATT&CK matrix and see a giant spreadsheet of doom. Rows and columns of technique IDs that make your eyes glaze over. That’s because nobody explains the hierarchy properly:
Tactics = The why. What the attacker is trying to accomplish (gain access, move laterally, steal data).
Techniques = The how. The specific method used to achieve that tactic (phishing, credential dumping, process injection).
Sub-techniques = The specific how. The granular variant (spearphishing attachment vs. spearphishing link vs. spearphishing via service).
Procedures = The exact how. What a specific threat group did in a specific incident (APT29 used OAuth tokens to maintain persistence in a specific campaign).
Translation: Tactics are the chapters. Techniques are the pages. Sub-techniques are the paragraphs. Procedures are the footnotes from real life.
Show Image
The 14 ATT&CK Tactics – What Attackers Actually Do (In Order)
Before you can use MITRE ATT&CK for pentesting, you need to understand the 14 tactics in the Enterprise matrix. Not the marketing version – the real-world version.
| # | Tactic | What It Actually Means | Pentest Relevance |
|---|---|---|---|
| 1 | Reconnaissance | Googling your target (but systematically) | OSINT, subdomain enum, LinkedIn scraping |
| 2 | Resource Development | Setting up attack infrastructure | C2 servers, phishing domains, tool prep |
| 3 | Initial Access | Getting your foot in the door | Phishing, exploiting public apps, stolen creds |
| 4 | Execution | Running malicious code | PowerShell, scripting, command-line abuse |
| 5 | Persistence | Staying in after reboot | Web shells, scheduled tasks, registry mods |
| 6 | Privilege Escalation | Going from user to admin | Kernel exploits, misconfigs, token manipulation |
| 7 | Defense Evasion | Hiding from security tools | Obfuscation, disabling AV, process injection |
| 8 | Credential Access | Stealing passwords and tokens | Mimikatz, credential dumping, keylogging |
| 9 | Discovery | Mapping the internal network | AD enumeration, network scanning, file browsing |
| 10 | Lateral Movement | Jumping between machines | Pass-the-hash, RDP, remote services |
| 11 | Collection | Gathering data to steal | Screenshots, keystrokes, database dumps |
| 12 | Command & Control | Talking to your attack server | Encrypted channels, DNS tunneling, web protocols |
| 13 | Exfiltration | Getting data out | Cloud uploads, encrypted transfers, steganography |
| 14 | Impact | Breaking things or demanding ransom | Encryption, defacement, data destruction |
The critical insight most people miss: Real attacks don’t follow this order linearly. An attacker might jump from Initial Access straight to Discovery, skip Persistence entirely, loop back to Credential Access, and then hit Lateral Movement three times.
That’s exactly why ATT&CK uses a matrix and not a flowchart. It’s not a kill chain. It’s a menu.
Why MITRE ATT&CK Pentesting Is Different From Regular Pentesting
Let’s be real. Most penetration tests follow the same tired script:
- Run Nessus or Qualys
- Find some CVEs
- Try to exploit a few
- Write a report with “Critical”, “High”, “Medium” labels
- Client ignores 60% of findings
- Repeat next quarter
That’s vulnerability assessment dressed up as pentesting. And it’s why organizations keep getting breached despite “passing” their annual pentest.
ATT&CK-based pentesting is fundamentally different because it focuses on behaviors, not vulnerabilities.
Instead of asking “what CVEs exist?”, you’re asking “what would APT28 do if they got into this network?”
| Traditional Pentesting | ATT&CK-Based Pentesting |
|---|---|
| Find vulnerabilities | Simulate adversary behaviors |
| CVE-focused | TTP-focused |
| Point-in-time snapshot | Maps to ongoing detection |
| “We found 47 highs” | “We tested 23 techniques across 8 tactics” |
| Report sits on a shelf | Report directly improves SOC detection |
| Passes compliance checkbox | Actually tests if defenses work |
| Tool-driven (run scanner, get results) | Intelligence-driven (model threat, test techniques) |
Here’s why this matters: when you map your pentest to ATT&CK technique IDs, your blue team can take those exact IDs and check whether their SIEM, EDR, and SOC actually detect them.
That’s the bridge between offense and defense that 99% of organizations are missing.
Show Image
How to Plan a Pentest Using MITRE ATT&CK – Step by Step
Enough theory. Here’s how you actually do this.
Step 1: Identify Your Threat Landscape
Before you touch a keyboard, figure out who is likely to attack your organization.
Go to the ATT&CK Groups page (attack.mitre.org/groups/) and find threat actors relevant to your industry. Finance? Look at FIN7, FIN8, Carbanak. Healthcare? Lazarus Group, APT41. Government? APT28, APT29, Turla.
Each group has a documented list of techniques they use. That’s your starting point.
Pro tip: Use the MITRE ATT&CK Navigator (mitre-attack.github.io/attack-navigator/) to create a heatmap. Overlay multiple threat groups and you’ll see which techniques show up repeatedly. Those are your priority testing targets.
Step 2: Map Techniques to Your Test Plan
Take the top 15-20 techniques from your threat analysis and create a test plan. Here’s what a partial plan looks like:
| Tactic | Technique ID | Technique | Test Method | Tool |
|---|---|---|---|---|
| Initial Access | T1190 | Exploit Public-Facing App | Test web apps for SQLi, RCE | Burp Suite, sqlmap |
| Initial Access | T1566.001 | Spearphishing Attachment | Send test phishing emails | GoPhish |
| Execution | T1059.001 | PowerShell | Test PowerShell execution policies | Custom scripts |
| Persistence | T1053.005 | Scheduled Task | Create persistence via task scheduler | schtasks.exe |
| Priv Escalation | T1068 | Exploitation for Priv Esc | Test kernel and service exploits | Local exploit scripts |
| Credential Access | T1003.001 | LSASS Memory Dump | Attempt credential extraction | Mimikatz, ProcDump |
| Lateral Movement | T1021.001 | Remote Desktop Protocol | Test RDP access with stolen creds | xfreerdp, rdesktop |
| Defense Evasion | T1562.001 | Disable/Modify Tools | Attempt to disable EDR/AV | Custom payloads |
| Exfiltration | T1048 | Exfiltration Over Alt Protocol | Test DNS/ICMP data exfil | dnscat2, custom scripts |
Each test maps directly to an ATT&CK ID. This means your report isn’t just “we found RDP was misconfigured” – it’s “we successfully executed T1021.001 (Remote Desktop Protocol) under the Lateral Movement tactic, which is a technique actively used by APT29 and FIN7.”
That sentence carries 10x more weight in a boardroom.
Step 3: Execute and Document Everything Per Technique
During the engagement, document every action against its ATT&CK mapping:
- Technique ID: T1003.001
- Tactic: Credential Access
- What we did: Dumped LSASS memory using ProcDump
- Result: Successfully extracted 14 domain credentials including 2 admin accounts
- Detection: EDR did not alert. SIEM generated no event. SOC had zero visibility.
- Recommendation: Implement Credential Guard, configure LSASS as PPL, add SIEM rule for process access to LSASS
That last line is the gold. Your pentest finding now directly tells the blue team what to build.
Step 4: Create an ATT&CK Navigator Heatmap
After the engagement, create a Navigator layer showing:
- Green: Techniques the client detected and responded to
- Yellow: Techniques the client detected but didn’t respond to
- Red: Techniques the client completely missed
This visual makes executive presentations stupidly simple. No more explaining CVE scores to a CFO. Just point at the red spots and say “attackers can do all of this and nobody in your organization would notice.”
Show Image
Mapping Vulnerabilities to ATT&CK – The CVE-to-Technique Bridge
This is where most vulnerability management programs fall apart.
You’ve got a Qualys scan with 3,000 findings. Your CISO wants to know which ones matter. The answer isn’t “all the criticals” – it’s “the ones that map to techniques attackers actually use against organizations like yours.”
Here’s how to build the bridge:
The CVE → Technique Mapping Process
Step 1: Take a critical CVE. Let’s use a real example – a public-facing application RCE vulnerability.
Step 2: Map the exploitation to Initial Access → T1190 (Exploit Public-Facing Application).
Step 3: Now model the attack chain. If an attacker exploits this vulnerability, what happens next?
| Stage | Tactic | Likely Technique | Why |
|---|---|---|---|
| Entry | Initial Access | T1190 – Exploit Public-Facing App | The vulnerability gives them a foothold |
| Foothold | Execution | T1059 – Command/Scripting Interpreter | They’ll run commands via the exploited app |
| Survive | Persistence | T1505.003 – Web Shell | They’ll drop a web shell to maintain access |
| Escalate | Privilege Escalation | T1068 – Exploitation for Priv Esc | They’ll try to escape app-level permissions |
| Expand | Discovery | T1046 – Network Service Discovery | They’ll scan the internal network |
| Spread | Lateral Movement | T1021 – Remote Services | They’ll jump to other systems |
| Steal | Exfiltration | T1041 – Exfil Over C2 Channel | They’ll pull data through their command channel |
This is how you turn “CVE panic” into a detection plan. Instead of just patching the CVE (which you should still do), you also build detections for every step in that chain. Even if the CVE gets exploited, your SOC catches the attacker at step 3, 4, or 5.
That’s defense in depth. Not the buzzword – the real thing.
2026 Attack Trends You Need to Know
According to the Picus Red Report 2026, the top techniques attackers use have shifted dramatically:
- T1055 (Process Injection) is the #1 most observed technique
- 8 out of 10 top techniques focus on Defense Evasion and Persistence – attackers care more about staying hidden than causing immediate damage
- T1486 (Data Encrypted for Impact) – ransomware deployment – dropped 38% year-over-year as attackers shift from encryption to pure data theft
Translation: Modern attackers aren’t smashing and grabbing. They’re moving in, setting up shop, and living in your network for months. Your pentesting needs to reflect that reality.
MITRE ATT&CK for Defense – Building Detections That Actually Work
So yeah, ATT&CK isn’t just for red teams. It’s actually more powerful on the blue side.
Gap Analysis: Where Are You Blind?
Take the full ATT&CK Enterprise matrix. For each technique, ask three questions:
- Can we prevent it? (Do we have a control that blocks this technique?)
- Can we detect it? (Do we have a SIEM rule, EDR detection, or alert for this technique?)
- Can we respond to it? (Do we have a playbook if this technique triggers?)
Map the answers in ATT&CK Navigator. The red spots are where attackers will live rent-free in your network.
Building Detection Rules Per Technique
Here’s a practical example. You want to detect T1003.001 (LSASS Memory Credential Dumping):
What to monitor:
- Process access to lsass.exe with PROCESS_VM_READ permissions
- ProcDump, comsvcs.dll, or Mimikatz execution patterns
- Suspicious process creation targeting lsass.exe PID
SIEM rule logic (pseudo-code):
IF process_access.target_name == "lsass.exe"
AND process_access.granted_access CONTAINS "0x1010" OR "0x1FFFFF"
AND process_access.source_name NOT IN [known_legitimate_processes]
THEN ALERT: "Potential LSASS Credential Dumping - T1003.001"
SEVERITY: CriticalWhat most SOCs get wrong: They build the rule but never test it. Run the technique in a lab, verify the alert fires, then deploy. Untested detections are decoration.
Show Image
XHack SOC – ATT&CK-Powered Threat Detection in Action

Let’s be real – I’m about to plug our own platform. But since I’m cursed with brutal honesty, I’ll tell you exactly what it does and where it falls short.
XHack SOC is an AI-powered Security Operations Center that we built because most SIEM/SOC solutions are either overpriced enterprise nightmares or glorified log viewers that require a PhD to configure.
What XHack SOC Actually Does
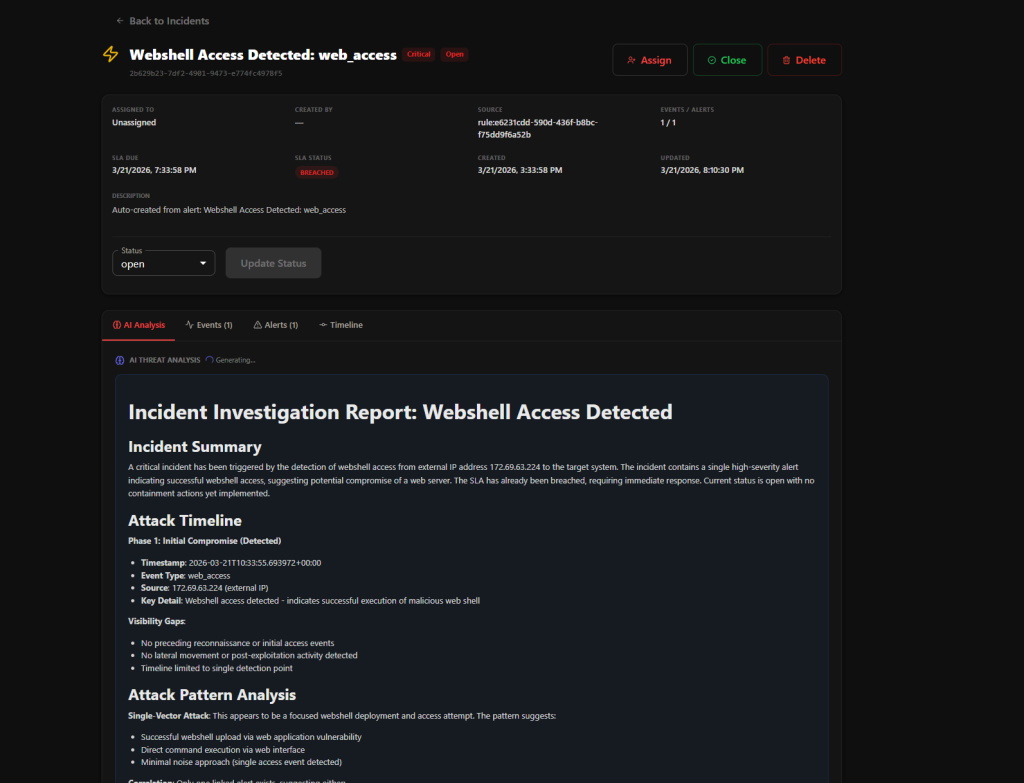
During our live production testing, XHack SOC generated 10+ security alerts across multiple servers while running against real production environments and live websites. The system detected multiple attack patterns with near-zero false positives, automatically organizing everything into AI-powered attack chains, detailed alerts, and structured reports.

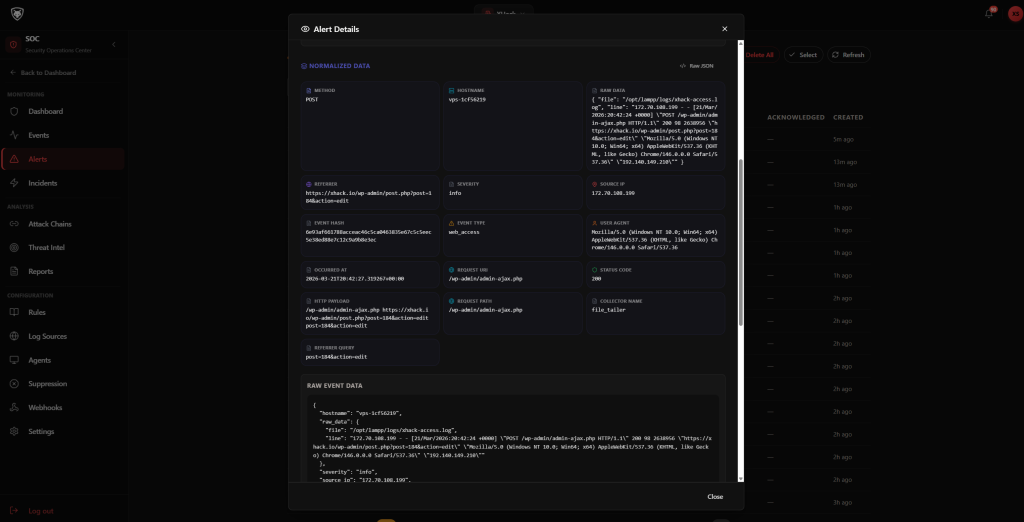
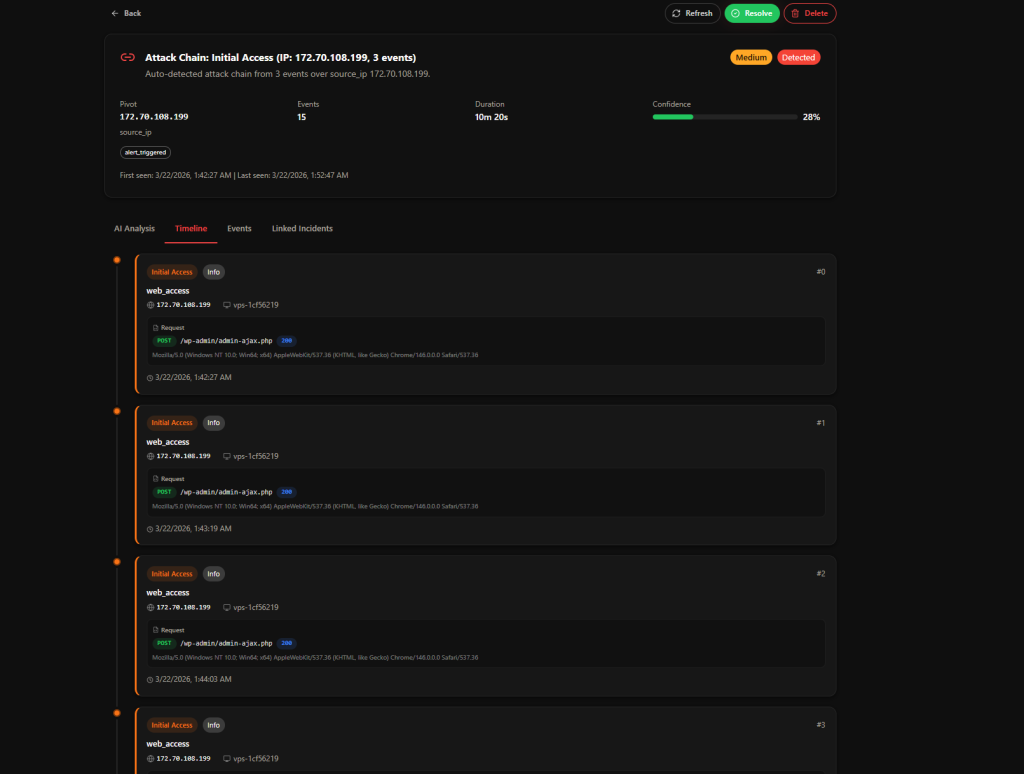
Here’s what makes it relevant to this article: XHack SOC maps detections directly to MITRE ATT&CK techniques.
When a threat is detected, you don’t just get “suspicious activity on port 443.” You get:
- Attack technique: T1190 – Exploit Public-Facing Application
- Tactic mapping: Initial Access
- Attack chain: Full visualization from initial exploit to post-exploitation behavior
- AI-generated remediation: Specific steps to contain and fix the issue
- Automated incident creation: No manual ticket writing
Key Features for ATT&CK-Based Security
- Real-time threat detection – Continuous monitoring across your infrastructure
- AI-powered attack chain reconstruction – Automatically connects related events into coherent attack narratives
- Custom detection rules – Create rules using AI to defend against targeted attacks specific to your environment
- Automated alerting system – Alerts via email, n8n, webhooks, or any integration you configure
- XHack AI analysis – Intelligent security analysis and automated remediation guidance
- Centralized SOC visibility – Single dashboard for all your log monitoring and threat data
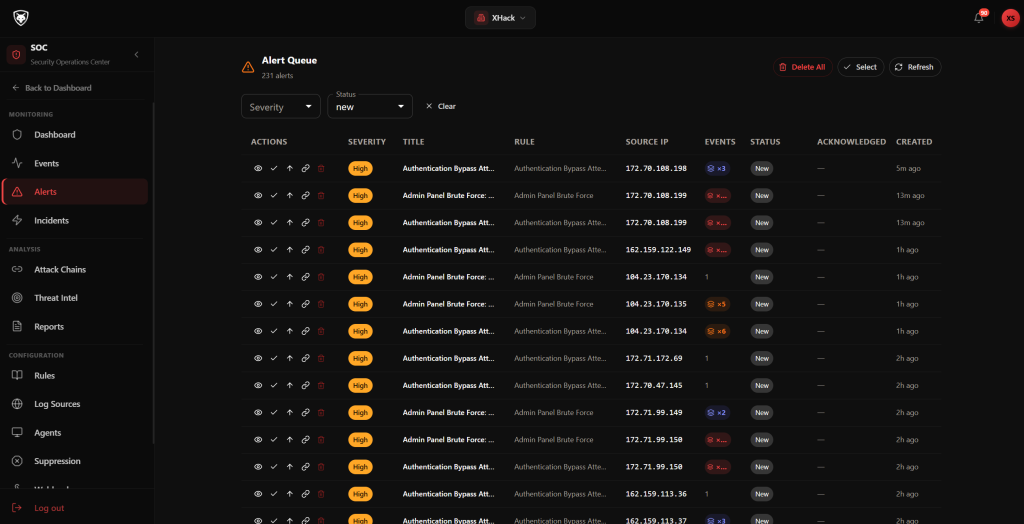
How XHack SOC Uses ATT&CK in Practice
Instead of analysts spending hours correlating logs and events, XHack SOC does the heavy lifting in the background.
Here’s the actual workflow:
- Activity detected → XHack AI analyzes the behavior
- ATT&CK mapping → Technique and tactic automatically identified
- Chain analysis → Related events linked into a complete attack narrative
- Alert generated → Sent via email/n8n/webhook with full context
- Remediation provided → AI-generated fix instructions specific to the incident
What the SOC analyst actually needs to do? Review the alert, take action, and report if necessary. That’s it.
No manual log digging. No complex correlation work. No wasted hours.
XHack SOC Custom Rules – ATT&CK-Aligned Detection
This is where it gets interesting for ATT&CK-based defense:
You can create custom detection rules using AI to defend against unique and targeted attacks specific to your environment. Want to detect a specific T1053 (Scheduled Task) persistence technique that targets your infrastructure? Build a custom rule in minutes, not days.
The platform’s Threat Intelligence capabilities:
- Detect attacks in real time
- Generate AI-powered remediation guidance
- Automatically create alerts and incidents
- Track complete attack chains from initial access to impact
- Adapt detection using intelligent custom rules
Everything runs in the background, continuously monitoring and analyzing activity. When something important happens, you get instant alerts via email or through any integrations you’ve configured.
What XHack SOC Won’t Do (Honest Assessment)
Since I promised brutal honesty:
- It won’t replace your security team – AI removes the noise and lets analysts focus on real threats, but human judgment is still required for complex decisions
- It’s not a silver bullet for compliance – You still need policies, procedures, and governance frameworks
- Custom rules require understanding – The AI helps you build rules, but you need to know what you’re defending against to build effective ones
But here’s what it changes: Security teams don’t have to stare at screens 24/7 anymore. The AI handles detection and correlation. Humans handle decisions and response.
That’s the future of SOC operations – AI-driven defense, not AI replacement.
Practical ATT&CK Implementation – A Real-World Pentest Walkthrough
Let me walk you through how a MITRE ATT&CK pentest actually plays out. Not theory – a sanitized but real engagement structure.
Scenario: Testing a Mid-Size Company’s Defenses
Target: Company with 500 employees, hybrid cloud (Azure AD + on-prem), web applications, and a SOC using a commercial SIEM.
Threat model: FIN7-style attack (financially motivated, targets corporate environments).
Phase 1: Reconnaissance (T1592, T1589, T1593)
What we did:
- Scraped LinkedIn for employee names and roles (T1593.001 – Social Media)
- Enumerated subdomains and discovered 14 web applications (T1596 – Search Open Technical Databases)
- Found 3 employees’ email format from breach data (T1589.002 – Email Addresses)
What the client detected: Nothing. Zero alerts. Recon is almost always invisible to defenders.
Phase 2: Initial Access (T1566.001, T1190)
What we did:
- Sent targeted phishing emails to 8 employees with a payload disguised as an invoice (T1566.001)
- 3 out of 8 clicked. 1 entered credentials on our phishing page.
- Simultaneously tested a vulnerable API endpoint we found during recon (T1190)
What the client detected: Email gateway flagged 2 phishing emails. The API exploitation generated zero alerts.
Phase 3: Execution + Persistence (T1059.001, T1053.005)
What we did:
- Used stolen credentials to access VPN
- Executed PowerShell commands to enumerate the domain (T1059.001)
- Created a scheduled task for persistence (T1053.005)
What the client detected: EDR flagged PowerShell execution but classified it as “low severity.” The SOC didn’t investigate. The scheduled task went completely unnoticed.
Phase 4: Credential Access + Lateral Movement (T1003.001, T1021.001)
What we did:
- Dumped credentials from LSASS using a custom tool (T1003.001)
- Used admin credentials to RDP into 3 additional servers (T1021.001)
- Accessed a file server with sensitive financial data
What the client detected: The credential dump triggered no alerts. RDP sessions were logged but nobody reviewed them. File server access was completely invisible.
Final Results: ATT&CK Coverage Heatmap
| Tactic | Techniques Tested | Detected | Blocked | Blind |
|---|---|---|---|---|
| Reconnaissance | 3 | 0 | 0 | 3 |
| Initial Access | 2 | 1 | 0 | 1 |
| Execution | 1 | 1 (low sev) | 0 | 0 |
| Persistence | 1 | 0 | 0 | 1 |
| Credential Access | 1 | 0 | 0 | 1 |
| Lateral Movement | 1 | 0 | 0 | 1 |
| Total | 9 | 2 (22%) | 0 (0%) | 7 (78%) |
Translation: The company was blind to 78% of techniques an attacker would use. Their expensive SIEM and EDR stack caught almost nothing. And this is a mid-size company that thought their security was “pretty good.”
This is why ATT&CK-based pentesting matters. Traditional pentesting would have found the vulnerable API and the missing email filters. ATT&CK-based pentesting showed that even after getting caught at the door, an attacker could do whatever they wanted inside.
Show Image
ATT&CK Tools and Resources You Should Be Using
For Red Teams / Pentesters
| Tool | Purpose | ATT&CK Integration |
|---|---|---|
| MITRE ATT&CK Navigator | Visualize technique coverage | Create layers, compare threat actors |
| MITRE Caldera | Automated adversary emulation | Executes ATT&CK techniques automatically |
| Atomic Red Team | Individual technique testing | One atomic test per ATT&CK technique |
| Cobalt Strike | Commercial C2 framework | Maps operations to ATT&CK IDs |
| Sliver | Open-source C2 | Modern alternative with ATT&CK mapping |
For Blue Teams / SOC
| Tool | Purpose | ATT&CK Integration |
|---|---|---|
| XHack SOC | AI-powered threat detection | Auto-maps detections to ATT&CK techniques |
| Sigma Rules | Universal detection rules | Each rule maps to ATT&CK technique IDs |
| MITRE D3FEND | Defensive technique catalog | Maps defenses against ATT&CK techniques |
| ATT&CK Evaluations | Vendor testing program | Tests EDR/XDR against real ATT&CK techniques |
For Both
| Tool | Purpose | ATT&CK Integration |
|---|---|---|
| ATT&CK Workbench | Customize your own ATT&CK instance | Add custom techniques, groups, software |
| VERIS-to-ATT&CK Mapping | Connect incidents to techniques | Bridge incident data to ATT&CK framework |
FAQ – MITRE ATT&CK Pentesting Questions Answered
How is MITRE ATT&CK different from the Cyber Kill Chain?
The Cyber Kill Chain (Lockheed Martin, 2011) treats attacks as a linear sequence of 7 phases – reconnaissance through actions on objectives. ATT&CK doesn’t assume a fixed order. Real attacks skip phases, loop back, and execute multiple tactics simultaneously. The Kill Chain helps you understand progression conceptually, but ATT&CK gives you technique-level detail needed to build specific detections. For MITRE ATT&CK pentesting, the non-linear approach is critical because it lets you simulate realistic attack patterns, not textbook sequences.
Can a small team implement ATT&CK-based pentesting?
Yes, but prioritize ruthlessly. You don’t need to test all 203 techniques. Start with the top 10-20 techniques relevant to your threat landscape. Use Atomic Red Team for quick technique testing – each test is a single script or command that validates one technique. A team of 2-3 can run a meaningful ATT&CK-based assessment in 1-2 weeks by focusing on the techniques that matter most to their organization.
How does MITRE ATT&CK pentesting work with AI-powered SOCs like XHack?
This is where it gets powerful. When your red team tests technique T1003.001 (LSASS dumping), an AI-powered SOC like XHack SOC should detect it, map it to the correct ATT&CK technique, generate an alert with context, and suggest remediation – all automatically. The pentest validates whether the AI detection actually works. If the SOC misses it, you know exactly which detection rule to build. If it catches it, you have documented proof that your defense works against that specific technique.
What’s the minimum ATT&CK coverage a company should aim for?
There’s no magic number, but start with the MITRE ATT&CK top techniques report (published annually). Covering the top 20 most commonly used techniques gives you defense against the majority of observed attacks. The Picus Red Report 2026 shows that 8 of the top 10 techniques focus on Defense Evasion and Persistence – so if you’re only monitoring Initial Access, you’re blind to what attackers do after they get in.
Conclusion
That’s a wrap on MITRE ATT&CK pentesting and vulnerability management.
The framework isn’t complicated. The industry just makes it complicated because complexity sells consulting hours.
The core idea is simple: Know what attackers do (ATT&CK techniques). Test whether your defenses catch it (pentesting). Fix the gaps (detection engineering). Repeat.
If you want AI-powered detection that maps directly to ATT&CK techniques and removes the manual correlation nightmare, XHack SOC does exactly that. Not perfectly – nothing is – but it’s the closest thing to having a SOC analyst that never sleeps, never gets alert fatigue, and never misses a correlation.
Security operations are evolving from manual monitoring to AI-driven defense. The teams that adopt this shift will detect faster, respond smarter, and actually sleep at night.
The ones that don’t? They’ll keep staring at dashboards, drowning in alerts, and wondering why they got breached despite spending six figures on security tools.
Think I missed something? Got a better ATT&CK workflow? Hit me up on LinkedIn – I respond to everything, including the people who think AI-powered SOCs are overhyped. (You’re wrong, but I’ll explain why politely.)
