How to choose a pentest provider is the single most expensive decision most security teams get wrong. And nobody warns you until after you’ve wasted $15K on a glorified Nessus scan with a fancy logo.
Here’s the reality. The penetration testing market is projected to hit $5 billion by 2030. That kind of money attracts serious talent AND serious charlatans. 92% of organizations increased their cybersecurity budgets last year. 85% boosted spending on pentesting specifically. That’s a lot of checks being written to companies that range from world-class to borderline fraudulent.
I went through real client horror stories, industry reports, vendor red flags, and actual scam documentation to build the guide I wish existed when I first started evaluating pentest providers. Nobody’s doing the homework. So I did.
Let’s get into it.
Table of Contents
- Why Most Companies Pick the Wrong Pentest Provider
- Vulnerability Scan vs. Penetration Test: The $15,000 Scam
- 9 Questions to Ask Before You Hire a Pentest Provider
- Certifications That Actually Matter (And Ones That Don’t)
- How to Choose a Pentest Provider by Company Size
- Red Flags That Scream “Run”
- Pentest Provider Comparison: What to Evaluate
- What a Good Pentest Report Actually Looks Like
- How XHack Approaches Penetration Testing
- FAQ
Why Most Companies Pick the Wrong Pentest Provider
Most companies pick a pentest provider the same way they’d pick a plumber. Google it, check the reviews, go with whoever sounds legit and doesn’t charge too much.
That approach gets you burned.
The average cost of a data breach in the U.S. is now $10.22 million (IBM, 2025). A proper pentest costs $10,000 to $50,000. That’s an ROI of over 200:1 if it catches even one exploitable vulnerability before an attacker does.
But here’s what nobody tells you. A bad pentest is worse than no pentest. It gives you a false sense of security. You check the compliance box, your board feels warm and fuzzy, and six months later you’re on the front page because the “tested” system had a critical flaw the vendor never actually tested for.
73% of successful cyber perimeter breaches in 2025 were due to vulnerable web applications. Not misconfigurations. Not phishing. Applications. If your pentest provider didn’t thoroughly test your web apps with manual techniques, they missed the biggest attack vector.

Vulnerability Scan vs. Penetration Test: The $15,000 Scam
This is the single biggest fraud in the cybersecurity industry and it happens every single day.
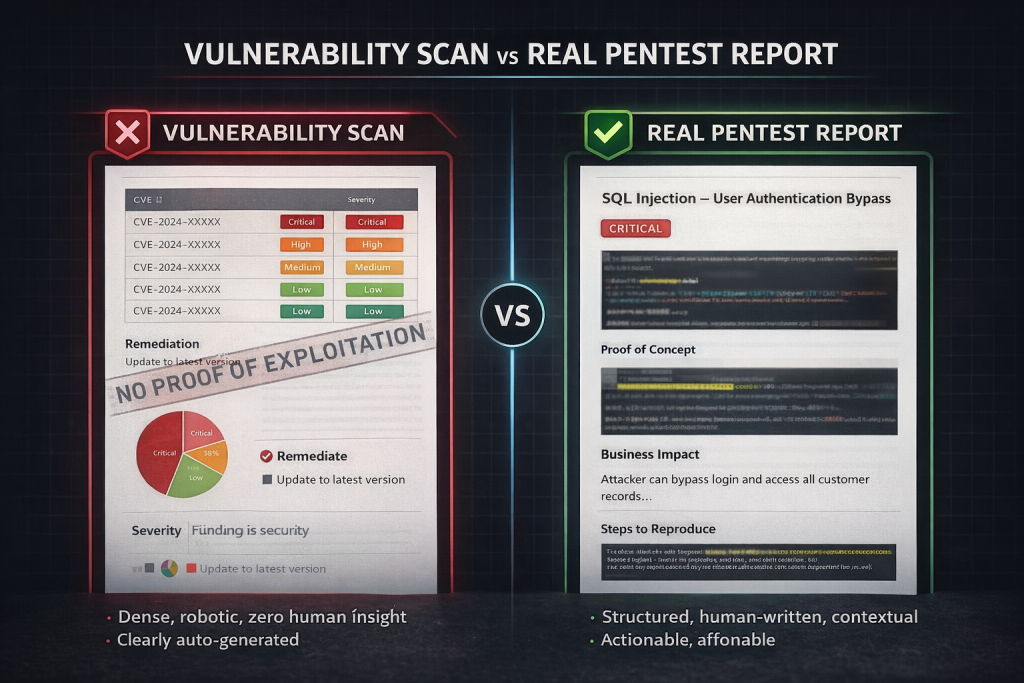
Companies pay $10,000 to $30,000 for a “penetration test” and receive a vulnerability scan. The vendor runs Nessus or Qualys, exports the report, slaps their logo on it, and calls it a pentest. The client doesn’t know the difference. The auditor doesn’t check. Everyone moves on until the breach happens.
Here’s how to tell the difference:
| Factor | Vulnerability Scan | Real Penetration Test |
|---|---|---|
| Methodology | Automated tools only | Manual testing + tools |
| Duration | Hours | 1 to 4 weeks |
| Cost | $500 to $3,000 | $10,000 to $50,000+ |
| Output | List of CVEs | Proof-of-concept exploits with business impact |
| Exploitation | None. Just identifies potential issues | Actively exploits vulnerabilities to prove impact |
| Business Logic Testing | Impossible (automated can’t understand logic) | Core focus of manual testing |
| Compliance Value | Does NOT satisfy PCI DSS, SOC 2, or ISO 27001 | Meets regulatory requirements |
| False Positives | High | Low (validated through manual testing) |
The dead giveaway? If your “pentest report” is mostly automated output with CVE numbers and zero screenshots of actual exploitation, you paid for a scan. Period.
A real pentest involves humans actively exploiting weaknesses, chaining multiple vulnerabilities together, testing business logic flaws, and demonstrating exactly what an attacker could steal, break, or access. That’s what you’re paying for. Not a PDF of known vulnerabilities.
9 Questions to Ask Before You Hire a Pentest Provider
When figuring out how to choose a pentest provider, these nine questions will separate the real operators from the pretenders faster than anything else.
Question 1: “What percentage of your testing is manual vs. automated?”
If the answer is anything less than 60% to 70% manual, walk away. Automated tools are part of the process, but they should be the starting point, not the entire engagement. The best providers allocate automated scanning to roughly 5% to 10% of the engagement and spend the rest on manual exploitation, logic testing, and creative attack chains.
Question 2: “Can I see a sample report?”
This is the ultimate filter. Any reputable firm will share a redacted sample report. If they won’t, that’s a red flag the size of Texas.
What to look for in the sample: proof-of-concept screenshots showing actual exploitation, business impact analysis for each finding, step-by-step remediation guidance, risk ratings tailored to YOUR context (not just generic CVSS scores), and an executive summary a non-technical person can understand.
Question 3: “Which specific people will be testing my systems, and what are their certifications?”
Notice I said “specific people,” not “our team has.” Firms love to list impressive credentials on their website while sending junior analysts to do your actual test.
Ask for names. Ask for LinkedIn profiles. Verify certifications directly with certifying bodies. This matters more than anything else about how to choose a pentest provider.
Question 4: “How do you scope engagements?”
Good providers scope based on your actual attack surface, business objectives, and risk profile. They’ll ask detailed questions about your environment, user roles, technology stack, and compliance requirements.
Bad providers scope by counting IP addresses or URLs and quoting a flat rate. That’s not scoping. That’s guessing.
Question 5: “What happens after you deliver the report?”
The engagement shouldn’t end when the PDF hits your inbox. Ask about remediation support, debrief calls, retesting, and whether they’ll help your developers understand the findings.
The best firms include a live walkthrough of findings with your technical team and offer retesting (sometimes included, sometimes at reduced cost) to verify your fixes actually work.
Question 6: “How do you handle scope creep and new discoveries?”
During a pentest, testers sometimes discover assets or attack paths outside the original scope. How the provider handles this tells you a lot about their integrity.
Good answer: “We’ll document it, notify you immediately, and discuss whether to expand scope.”
Bad answer: “We stick strictly to the agreed IPs.” (This means they’ll ignore critical findings that fall outside the contract.)
Question 7: “Can you provide references from companies in my industry?”
Industry-specific experience matters enormously. Pentesting a healthcare system with HL7 interfaces is fundamentally different from pentesting a fintech API. A provider who’s great at one may be mediocre at the other.
Ask for 2 to 3 references. Actually call them. Ask specifically about communication quality, report usefulness, and whether the findings actually helped prevent incidents.
Question 8: “What’s your testing methodology?”
You want to hear specific frameworks: OWASP Testing Guide, PTES, NIST SP 800-115, OSSTMM. But you also want to hear that they go beyond checklists with creative, adversarial thinking.
The best answer combines both: structured methodology for thoroughness AND hacker mindset for finding what checklists miss.
Question 9: “What differentiates a real finding from your report vs. what an automated scanner would catch?”
This question exposes whether the testers actually add value beyond running tools. A strong provider will immediately give you examples of business logic flaws, chained exploits, or authorization bypasses that no scanner could ever find.
If they stumble on this, their “pentest” is probably a scan with extra steps.
Certifications That Actually Matter (And Ones That Don’t)
Not all certifications are created equal when you’re learning how to choose a pentest provider. Some prove genuine hands-on hacking ability. Others prove you can pass a multiple-choice exam.
Certifications that prove real skill:
| Certification | Why It Matters | Difficulty |
|---|---|---|
| OSCP (Offensive Security Certified Professional) | 24-hour hands-on hacking exam. You actually have to break into systems | Very High |
| OSWE (Offensive Security Web Expert) | Advanced web application exploitation. Whitebox testing focus | Very High |
| CREST (CRT/CCT) | UK-standard practical exam. Recognized globally for rigor | High |
| GXPN (GIAC Exploit Researcher) | Advanced exploit development and penetration techniques | High |
| Burp Suite Certified Practitioner | Web security focused. Practical, hands-on exam | Moderate to High |
The certification that’s basically a meme:
CEH (Certified Ethical Hacker). I’m going to say what every experienced pentester thinks but most are too polite to say publicly. CEH is widely considered a joke in the offensive security community. It’s a multiple-choice exam that tests theory, not practice. Experienced practitioners openly mock it. If a firm leads with CEH as their primary credential, that tells you something about their depth of expertise.
What matters more than any certificate: look for providers whose testers publish research, contribute to open-source security tools, present at conferences (Black Hat, DEF CON, BSides), or have a track record of responsible vulnerability disclosures. That’s proof of real-world skill that no exam can replicate.
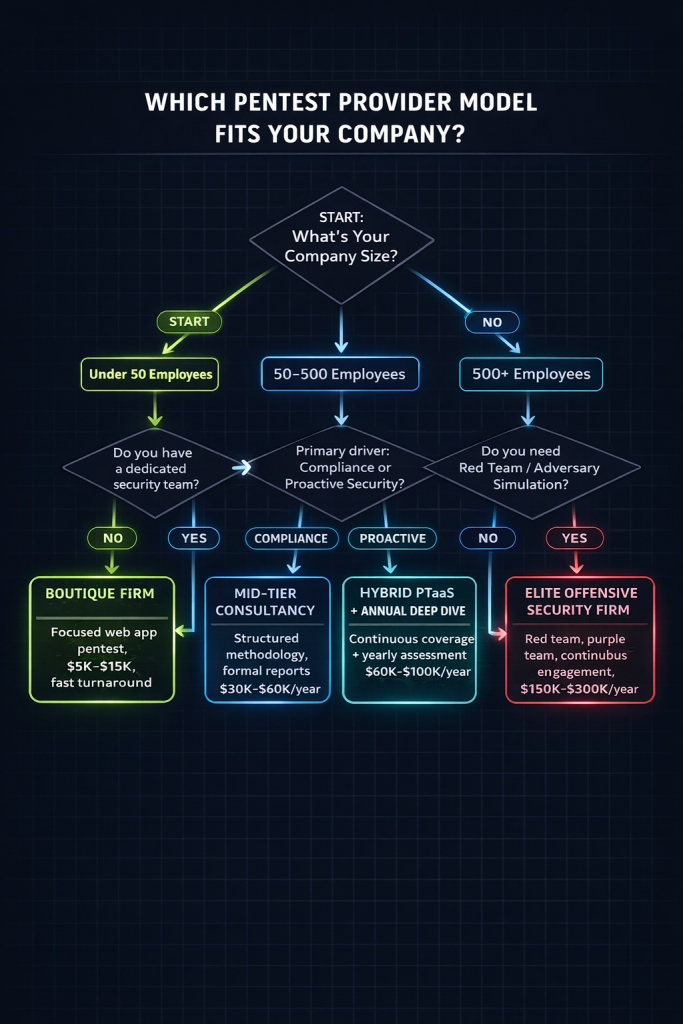
How to Choose a Pentest Provider by Company Size
Your company’s size, maturity, and regulatory requirements should dictate what kind of provider you need. Here’s the honest breakdown of how to choose a pentest provider based on where you actually are.
Startups (Under 50 Employees, Pre-Series B):
You probably need a focused web application pentest before your first enterprise client demands a SOC 2 report. Budget $5,000 to $15,000. Look for boutique firms or PTaaS platforms that understand SaaS architectures and can turn around results in 2 to 3 weeks. You don’t need a Big 4 firm. You need someone fast, thorough, and willing to explain findings to developers who’ve never read a pentest report.
Mid-Market (50 to 500 Employees, Established Revenue):
You need quarterly or semi-annual testing across web apps, APIs, cloud infrastructure, and possibly internal networks. Budget $30,000 to $100,000 annually. Consider PTaaS models for ongoing coverage supplemented by annual deep-dive assessments. This is where choosing the wrong provider hurts most because you’re big enough to be a target but may not have a dedicated security team to validate findings.
Enterprise (500+ Employees, Regulatory Obligations):
You need a provider who can handle complex, multi-environment engagements across cloud, on-prem, OT, and mobile. Budget $100,000+ annually. Red team engagements, purple team exercises, and continuous testing programs become essential. Insist on providers with CREST accreditation or equivalent and demand named senior testers for your engagement.
Red Flags That Scream “Run”
Knowing how to choose a pentest provider is as much about knowing what to avoid as what to look for. Here are the red flags that should make you close the tab immediately.
They quote without scoping. If a firm gives you a price after a 10-minute call without asking detailed questions about your environment, they’re guessing. And you’ll pay for that guess.
They promise results in days, not weeks. A real pentest of any meaningful scope takes 1 to 4 weeks minimum. If someone promises to pentest your enterprise web application in 2 days, they’re running a scan.
They won’t share sample reports. Every legitimate firm has redacted samples. No exceptions.
They rank themselves “#1 Pentest Company” on their own blog. Research has documented firms literally writing their own “top 10” lists, placing themselves first, and promoting those posts as objective rankings. Self-awarded rankings are marketing, not credibility.
They can’t name who will do the work. If they can’t tell you which testers will be assigned and what their qualifications are, assume the worst.
Their report is mostly Nessus/Qualys output. If 80%+ of the findings are straight from automated tool output with no manual validation or exploitation, you got scammed.
They get defensive when you ask hard questions. Some firms have reportedly threatened legal action against people who criticized their work. That’s not the behavior of a confident, capable provider.
The price seems too good to be true. A comprehensive web application pentest for $3,000? That’s not a deal. That’s an automated scan with a PDF.
Pentest Provider Comparison: What to Evaluate
When narrowing down how to choose a pentest provider, use this comparison framework to evaluate your shortlist.
| Criteria | What Good Looks Like | What Bad Looks Like |
|---|---|---|
| Testing Approach | 60 to 70%+ manual, creative exploitation | Mostly automated with minimal manual review |
| Team Credentials | OSCP, OSWE, CREST. Named testers assigned | CEH-only. “Our team” without naming individuals |
| Scoping Process | Detailed discovery call, tailored proposal | Flat rate based on IP count or URL count |
| Report Quality | PoC exploits, business impact, remediation steps | CVE lists, generic risk ratings, no exploitation proof |
| Post-Engagement | Debrief, retesting, remediation support | PDF delivered, engagement over |
| Methodology | OWASP, PTES, NIST + adversarial creativity | “Proprietary methodology” with no details |
| Communication | Dedicated PM, regular updates during testing | Radio silence until report delivery |
| Pricing Transparency | Clear breakdown of what’s included | Hidden retesting fees, scope creep charges |
| References | Happy to provide industry-specific references | Evasive or “confidential client list” |
| Sample Report | Freely shared, redacted | Won’t provide or “it’s proprietary” |
What a Good Pentest Report Actually Looks Like
The report is the deliverable. It’s what your board sees, your auditor reviews, and your developers use to fix things. A good report should include the following.
Executive Summary. Non-technical. Answers “how screwed are we?” in plain English. Includes overall risk rating and top 3 to 5 critical findings with business impact.
Methodology Section. Explains what was tested, how it was tested, what tools were used, and what was explicitly out of scope. This matters for compliance and for repeating the test later.
Detailed Findings. Each vulnerability documented with: a clear title, severity rating, proof-of-concept (screenshots, request/response pairs, commands used), business impact explanation, step-by-step remediation guidance, and references (CWE, OWASP, CVE where applicable).
Positive Findings. What’s working well. This matters for board reporting and morale. Good providers acknowledge strong controls alongside weaknesses.
Appendices. Raw tool output, full scan results, testing timelines, and tester credentials.
If your report doesn’t have proof-of-concept exploitation for critical and high findings, ask your provider what exactly they tested.
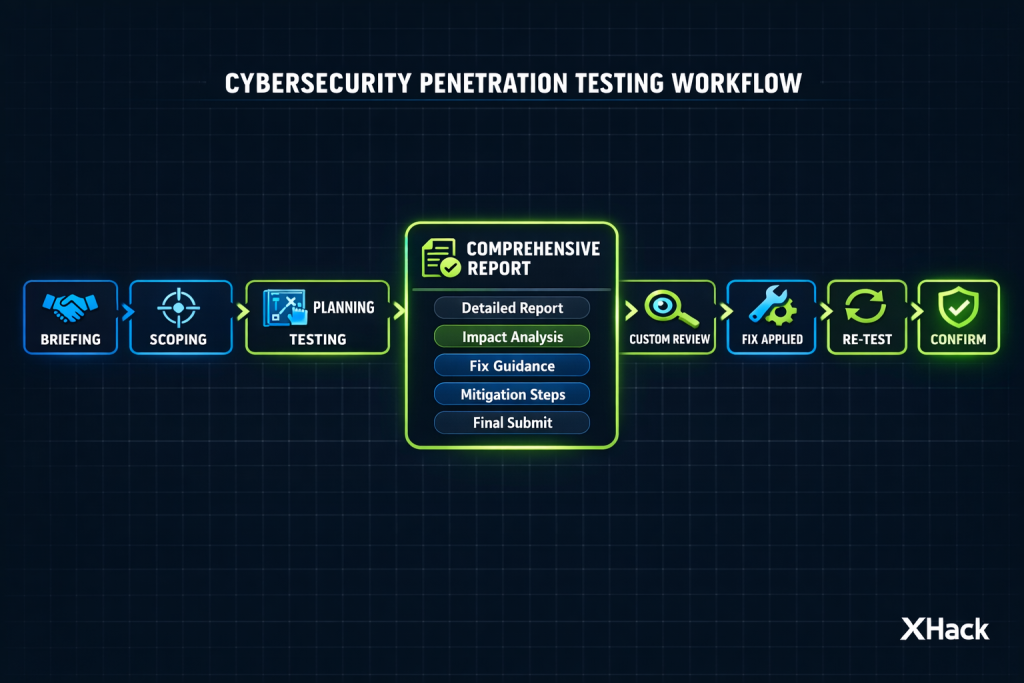
How XHack Approaches Penetration Testing
Look, I’m about to pitch our services. I’m biased. But since I’m cursed with brutal honesty, let me tell you exactly what we do AND where we have limitations.
What XHack does well:
Every engagement is 100% manual testing led by OSCP/OSWE-certified testers. No junior analysts running Nessus and calling it a day. We scope based on your actual environment, not a price sheet. Every finding comes with proof-of-concept exploitation, real business impact analysis, and remediation guidance your developers can actually follow.
We include a live debrief with your technical team after every engagement. We do retesting to verify your fixes actually work. And we’re transparent about what we tested, what we didn’t, and what fell outside scope.
What XHack doesn’t do (yet):
We’re not the right fit for massive enterprise red team engagements spanning 6+ months. We don’t do physical security testing. And we have a smaller team than the big PTaaS platforms, which means we book up fast during peak compliance seasons (Q4 is brutal). If you need immediate turnaround in under a week, we’ll be honest and tell you to look elsewhere rather than rush and deliver garbage.
Who should work with us:
SaaS companies, fintechs, healthtech startups, and mid-market companies who want a provider that treats their pentest like it actually matters. If you want a checkbox, we’re not your vendor. If you want to know exactly how an attacker would compromise your systems, let’s talk.
FAQ
How much does a penetration test cost in 2026?
A real penetration test costs between $5,000 and $50,000+ depending on scope and complexity. Web application tests average $12,500. Internal network tests average around $12,500 to $15,000. Cloud pentests run $10,000 to $50,000. Red team engagements start at $40,000. If someone quotes significantly below these ranges, verify you’re getting an actual pentest and not an automated scan.
How often should you do penetration testing?
At minimum, annually. Better practice is quarterly or after any significant infrastructure change, product launch, or acquisition. PCI DSS requires testing after any significant change to your environment. Over 70% of organizations have moved to continuous PTaaS models rather than one-off annual tests.
What’s the difference between a pentest and a vulnerability assessment?
A vulnerability assessment identifies potential weaknesses using automated tools. A penetration test goes further by actively exploiting those weaknesses to prove their impact, test business logic, and chain vulnerabilities together like a real attacker would. Both have value, but they serve different purposes and should never be confused or substituted for each other.
How do I know if my pentest provider is legitimate?
Ask for a sample report with proof-of-concept exploits. Verify individual tester certifications (OSCP, OSWE, CREST). Request references from companies in your industry. Confirm that testing is primarily manual. And check whether their report includes real exploitation evidence or just automated tool output.
Can I use a pentest report for SOC 2 or PCI DSS compliance?
Yes. SOC 2, PCI DSS, ISO 27001, and HIPAA all accept or require formal penetration testing reports. PCI DSS v4.0.1 mentions “penetration test” 75 times. The key requirement is that the test follows a structured methodology and produces a formal report with findings, risk ratings, and remediation guidance. Bug bounty reports typically do not satisfy these requirements.
The bottom line on how to choose a pentest provider: Stop shopping on price. Start shopping on proof. Ask the hard questions. Demand sample reports. Verify credentials. And if anything feels off, trust that instinct. A bad pentest doesn’t just waste money. It creates a dangerous illusion of security that could cost your company millions.
Follow Us on LinkedIn
