30-Second Summary: An enterprise security strategy in 2026 requires three pillars working together: dedicated VAPT engagements that validate real-world exploitability, a 24/7 SOC that detects and responds to threats in real time, and AI-powered tools that automate what humans can’t do at scale. Gartner projects global cybersecurity spending will hit $240 billion in 2026. Organizations with microsegmentation see 45% lower breach costs ($2.68M vs $4.88M average). Attackers now move laterally in 48 minutes after initial access (CrowdStrike 2025). 82% of exploited vulnerabilities required human reasoning and exploit chaining (Verizon DBIR 2025).
The average breach costs $4.88 million (IBM 2025). Ransomware payments jumped from $400,000 in 2023 to $2 to $3 million in 2025. Third-party involvement in breaches doubled from 15% to 30% year over year. This guide is XHack’s blueprint for building an enterprise security strategy that integrates all three pillars, with specific architecture guidance, real metrics, and how AI-powered platforms like XHack AI change what’s operationally possible.
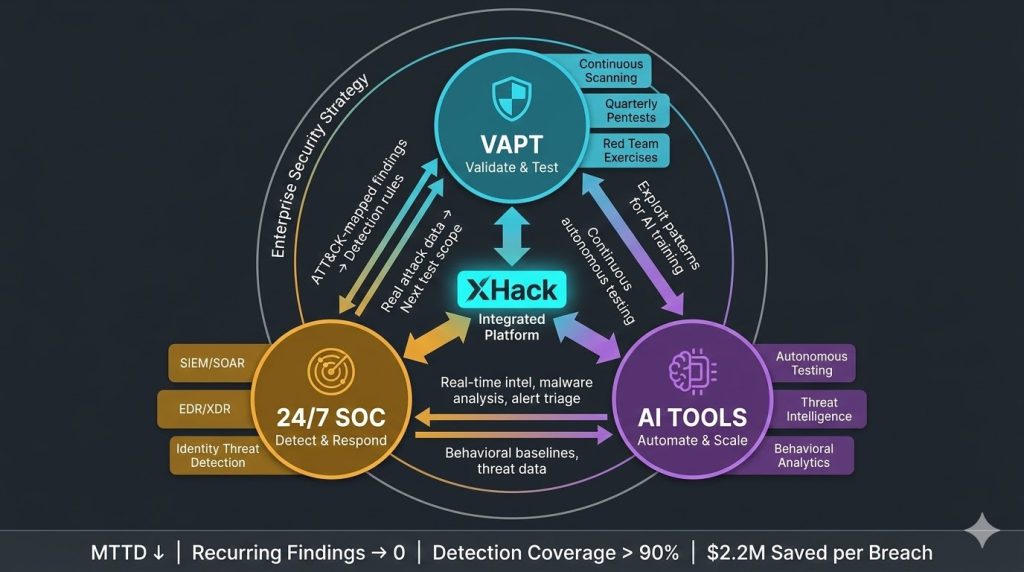
Enterprise security in 2026 has a structural problem: each pillar works fine in isolation. Together, most organizations run them as disconnected programs that share almost nothing.
Your VAPT team delivers a report. The SOC team files it. The AI tools run in their own dashboards. Nobody connects the pentest findings to the detection rules. Nobody feeds the SOC’s real-time threat data back into the next VAPT scope. Nobody uses AI to automate the bridge between identification and response.
The result is predictable. CrowdStrike’s 2025 Global Threat Report documented attackers reaching lateral movement in 48 minutes after initial access. 79% of detections were malware-free, meaning adversaries use hands-on-keyboard techniques that bypass traditional endpoint defenses entirely. If your VAPT, SOC, and AI tools aren’t feeding each other in real time, you have three separate programs and zero integrated defense.
This guide covers how to architect an enterprise security strategy where all three pillars reinforce each other, with practical implementation guidance, budget allocation frameworks, and how XHack’s AI-powered platform operationalizes the integration that most enterprises struggle to achieve manually.
Pillar 1: Dedicated VAPT Engagements
VAPT is the validation layer of your enterprise security strategy. Vulnerability assessments identify what’s potentially weak. Penetration tests prove what’s actually exploitable. Together, they provide the evidence base that everything else builds on.
Why Annual Testing Is No Longer Sufficient
The traditional model of annual penetration testing with quarterly vulnerability scans was designed for environments that changed slowly. Enterprise environments in 2026 deploy code multiple times per day, spin up cloud infrastructure on demand, and integrate new SaaS tools weekly. An annual pentest is a snapshot of an environment that no longer exists by the time the report is delivered.
The Verizon 2025 DBIR found that 20% of breaches began with exploited vulnerabilities. Edge device exploitation jumped eight-fold, from 3% to 22% of all breaches. Third-party involvement doubled from 15% to 30% year over year. Each of these trends means the attack surface changes faster than annual testing cycles can capture.
What Enterprise VAPT Architecture Looks Like
Continuous vulnerability scanning. Automated scanning runs against all internal and external assets on a continuous or weekly cycle. Credentialed scans provide accurate patch-level visibility. Results feed directly into the vulnerability management platform with SLA-driven remediation timelines: 72 hours for critical, 30 days for high, 90 days for medium.
Quarterly penetration testing. Focused manual testing rotates across the highest-risk attack surfaces each quarter: web applications in Q1, cloud infrastructure in Q2, internal network and Active Directory in Q3, and new deployments or acquisitions in Q4. Each engagement builds on the previous quarter’s findings.
Annual red team exercises. Full-scope adversary simulation testing the organization’s detection, response, and containment capabilities. Red team exercises test whether the SOC can detect and respond to a realistic attacker, not just whether vulnerabilities exist. Foundational red team engagements run $40,000 to $65,000. Advanced APT simulations run $70,000 to $120,000 or more.
Triggered testing. Any significant change (merger, acquisition, cloud migration, new application launch, major infrastructure change) triggers a scoped VAPT engagement within 30 days of deployment.
How XHack Delivers Enterprise VAPT
XHack provides certified VAPT services covering web applications, APIs, cloud infrastructure, internal/external networks, and mobile applications, all mapped to OWASP, NIST, and MITRE ATT&CK frameworks. What differentiates XHack at the enterprise level is the integration between manual expert testing and AI-powered automation.
XHack AI for autonomous penetration testing. XHack AI performs fully autonomous penetration testing: discovering attack surfaces, identifying vulnerabilities, crafting exploits, and generating professional reports without human intervention. This isn’t replacing manual testers. It’s running continuous AI-driven testing between quarterly manual engagements so the gap between assessments isn’t a blind spot.
XHack AI autonomous web browsing. The autonomous browsing engine controls a real browser to navigate websites, interact with web applications, discover vulnerabilities, and extract intelligence without human guidance. This catches vulnerabilities in dynamic, JavaScript-heavy applications that traditional scanners miss entirely.
XHack AI exploit development. XHack AI assists with the full exploit development lifecycle: vulnerability analysis through proof-of-concept creation, payload crafting, and weaponization for authorized security assessments. This accelerates the validation phase of penetration testing, producing exploit evidence in hours rather than days.
The practical impact: enterprises get continuous AI-powered testing supplemented by quarterly expert manual assessments, with full exploit validation and framework-mapped reporting.
Explore XHack AI capabilities.
Pillar 2: 24/7 Security Operations Center (SOC)
The SOC is the detection and response layer of your enterprise security strategy. VAPT tells you what’s vulnerable. The SOC tells you when someone is exploiting it.
The SOC Architecture for 2026
The modern enterprise SOC has evolved far beyond a room full of analysts watching dashboards. The 2026 SOC integrates SIEM/SOAR platforms, endpoint detection and response, network detection and response, identity threat detection, cloud security posture management, and AI-driven behavioral analytics into a unified detection and response pipeline.
SIEM and SOAR integration. The Security Information and Event Management platform aggregates logs from every source in the environment. The Security Orchestration, Automation, and Response layer automates playbook execution for known threat patterns. Together, they reduce mean time to detect (MTTD) and mean time to respond (MTTR) by automating the first 80% of incident triage so analysts focus on the 20% that requires human judgment.
Endpoint Detection and Response (EDR/XDR). Every endpoint (workstations, servers, mobile devices, cloud workloads) runs an agent that monitors process behavior, file activity, network connections, and registry changes. AI-powered behavioral detection identifies threats that signature-based tools miss. CrowdStrike’s Falcon, SentinelOne, and Microsoft Defender for Endpoint are the leading platforms, each using ML models trained on trillions of security events.
Network Detection and Response (NDR). Monitors east-west traffic within the network for lateral movement, command-and-control communication, and data exfiltration. With attackers reaching lateral movement in 48 minutes, NDR provides the detection layer that catches post-compromise activity before it reaches critical assets.
Identity Threat Detection (ITDR). Monitors authentication events, privilege escalation, and identity-based attacks. With 79% of detections being malware-free (CrowdStrike 2025), attackers increasingly use stolen credentials and living-off-the-land techniques. ITDR catches what EDR and NDR don’t see.
The Cost-Benefit Math
Building an in-house SOC requires 8 to 12 analysts for 24/7 coverage (accounting for shifts, vacations, and turnover), a SIEM platform ($100,000 to $500,000+ annually), EDR/XDR licensing, threat intelligence feeds, and ongoing training. Total cost: $1.5 million to $5 million per year for a mid-to-large enterprise.
Managed SOC services (MDR/MSSP) provide equivalent coverage for $500,000 to $1.5 million per year, with access to the vendor’s threat intelligence, tool stack, and analyst expertise. For enterprises that can’t justify the full in-house build, managed SOC is the pragmatic path.
The return on investment is clear. Organizations that deployed security AI and automation extensively saved an average of $2.2 million per breach compared to those that didn’t (IBM 2025). Mean time to identify and contain a breach dropped by 108 days for organizations with AI-powered SOC operations.
How XHack Integrates with SOC Operations
XHack’s platform doesn’t replace your SOC. It feeds it.
XHack AI threat intelligence. XHack AI provides real-time threat intelligence research, IOC (Indicator of Compromise) analysis, threat actor profiling, MITRE ATT&CK mapping, and automated intelligence report generation. This intelligence feeds directly into SOC detection rules, ensuring your monitoring is tuned to the threats that actually target your industry and infrastructure.
XHack AI malware analysis. When the SOC encounters a suspicious sample, XHack AI performs static and dynamic malware analysis: deobfuscating scripts, reversing binaries, extracting IOCs, classifying samples, and generating YARA detection rules. This turns a “suspicious file” alert into actionable intelligence with detection signatures in minutes rather than hours.
VAPT-to-SOC feedback loop. Every XHack VAPT engagement produces findings mapped to MITRE ATT&CK techniques. These mappings translate directly into SOC detection rules. If a pentest finds that lateral movement via Pass-the-Hash is possible in your Active Directory environment, the SOC should have a detection rule for PTH within 48 hours of the finding. XHack’s reporting structure is designed to make this handoff seamless.
Pillar 3: AI-Powered Security Tools
AI is the automation and scale layer of your enterprise security strategy. Humans provide judgment. VAPT provides validation. SOC provides detection. AI provides the speed and coverage that none of those can achieve manually.
Where AI Actually Delivers Value in 2026
The AI security market is crowded with marketing claims. Here’s where AI demonstrably changes outcomes based on real data.
Threat detection speed. AI-powered platforms detect threats in under one minute. Manual SOC triage takes 15 to 45 minutes per alert. When attackers reach lateral movement in 48 minutes, the difference between AI-speed and human-speed detection is the difference between containment and compromise.
Alert triage and false positive reduction. Enterprise SOCs generate thousands of alerts daily. Check Point reported 234 security incidents per organization per day in 2025. AI-driven triage reduces the noise by correlating alerts, assessing context, and prioritizing the 5% that require human investigation. Without AI, analysts drown in alerts and miss the real threats.
Automated response and containment. SOAR platforms with AI-driven playbooks can isolate compromised endpoints, block malicious IPs, revoke compromised credentials, and trigger forensic data collection automatically. Mean time to respond drops from hours to minutes for known threat patterns.
Continuous vulnerability assessment. AI-powered scanning identifies and prioritizes vulnerabilities in real time across the entire attack surface. Traditional scanning runs periodically. AI-driven platforms monitor continuously and alert when new exposures emerge.
Behavioral analytics. AI models baseline normal user and system behavior, then detect anomalies that indicate compromise: unusual login locations, abnormal data access patterns, privilege escalation sequences, and lateral movement indicators. This catches attacks that have no signature and match no known pattern.
The XHack AI Platform: Enterprise Security Strategy in Action
XHack AI isn’t a point tool. It’s a platform that operationalizes the integration between VAPT, SOC, and AI-driven automation. Here’s what it delivers across the enterprise security strategy:
Autonomous penetration testing. XHack AI discovers attack surfaces, identifies vulnerabilities, crafts exploits, and generates professional reports autonomously. This runs between manual pentest engagements, providing continuous validation rather than point-in-time snapshots. The AI handles reconnaissance, vulnerability identification, and exploitation while human testers focus on business logic, complex chaining, and scenario-based testing that AI can’t replicate.
Autonomous web browsing for application security. The browsing engine navigates web applications like a real attacker: clicking through workflows, submitting forms, testing authentication flows, and probing for injection points. It catches dynamic application vulnerabilities that traditional scanners miss because they can’t interact with modern JavaScript-heavy applications.
Exploit development assistance. From vulnerability analysis through proof-of-concept creation, payload crafting, and weaponization. This collapses the exploit validation timeline from days to hours, meaning VAPT reports are delivered faster with higher-quality evidence.
Real-time threat intelligence. IOC analysis, threat actor profiling, MITRE ATT&CK mapping, and automated intelligence reports. This feeds directly into SOC detection engineering, ensuring monitoring rules stay current with the evolving threat landscape.
Malware analysis. Static and dynamic analysis with deobfuscation, binary reversing, IOC extraction, sample classification, and YARA rule generation. SOC analysts get actionable intelligence from suspicious samples in minutes.
Full-service VAPT, red teaming, and SOC services. Beyond the AI platform, XHack provides certified human-led VAPT engagements, red team operations, 24/7 SOC monitoring, threat intelligence services, and compliance support (GDPR, SOC 2, ISO 27001, PCI DSS). Over 500 organizations trust XHack to deliver integrated security across all three pillars.

The Integration Architecture: How the Three Pillars Connect
The value of an enterprise security strategy isn’t in any single pillar. It’s in how they feed each other. Here’s the integration architecture:
VAPT feeds SOC. Every pentest finding mapped to MITRE ATT&CK translates into a SOC detection rule. If the pentest found exploitable SQL injection in the customer portal, the SOC monitors for SQL injection patterns on that endpoint. If the red team achieved lateral movement through Kerberoasting, the SOC deploys Kerberoasting detection.
SOC feeds VAPT. Real-world attack data from SOC operations informs the next VAPT scope. If the SOC detected phishing campaigns targeting finance employees, the next pentest includes social engineering against that department. If the SOC identified scanning activity against cloud APIs, the next assessment prioritizes API security testing.
AI accelerates both. AI-powered autonomous testing runs continuously between manual assessments. AI-driven threat intelligence keeps SOC detection current. AI-powered malware analysis provides rapid IOC extraction for both SOC response and VAPT context. AI-driven behavioral analytics detects what neither VAPT nor signature-based SOC monitoring can catch.
Metrics that prove integration is working: Mean time to detect (MTTD) should trend downward quarter over quarter. Percentage of VAPT findings with corresponding SOC detection rules should exceed 90%. Mean time from VAPT finding to SOC detection rule deployment should be under 72 hours. Recurring VAPT findings (same vulnerability found in consecutive tests) should trend toward zero.
Enterprise Security Strategy Budget Allocation
Gartner projects global cybersecurity spending at $240 billion in 2026, with enterprise allocation typically at 8% to 15% of IT budget. Here’s how to allocate within a security program:
Prevention and testing (VAPT): 15 to 20% of security budget. Continuous vulnerability scanning, quarterly penetration testing, annual red team exercises, and triggered assessments for significant changes.
Detection and response (SOC): 25 to 35% of security budget. SIEM/SOAR platform, EDR/XDR licensing, NDR, ITDR, 24/7 analyst coverage (in-house or managed), and threat intelligence feeds.
AI-powered tools and automation: 15 to 20% of security budget. AI-driven detection platforms, autonomous testing tools, SOAR playbook development, and behavioral analytics.
Personnel: 25 to 30% of security budget. Security leadership (CISO, security architects), SOC analysts, vulnerability management engineers, and compliance specialists.
Compliance and governance: 5 to 10% of security budget. Audit preparation, compliance tooling, policy development, and training programs.
Organizations with microsegmentation and integrated detection see 45% lower breach costs ($2.68M vs $4.88M average). Those deploying AI-powered security automation save $2.2 million per breach. The budget allocation above is designed to maximize both prevention and response ROI.
Frequently Asked Questions
What is the most important component of an enterprise security strategy?
No single component is sufficient. The data consistently shows that integrated programs outperform siloed ones. Organizations that deploy both proactive testing (VAPT) and AI-powered detection save $2.2 million more per breach than those relying on either alone (IBM 2025). However, if forced to prioritize, detection and response (SOC) provides the highest immediate impact because it operates continuously. VAPT validates periodically. AI accelerates both. The optimal enterprise security strategy layers all three with structured feedback loops between them.
How does AI-powered pentesting compare to manual penetration testing?
AI-powered pentesting like XHack AI’s autonomous testing platform excels at breadth, speed, and continuous coverage. It can scan entire attack surfaces, identify known vulnerability patterns, and generate exploit proof-of-concepts autonomously. Manual penetration testing excels at depth, creativity, and business logic analysis. Human testers find complex attack chains, application-specific logic flaws, and scenario-based vulnerabilities that AI currently can’t replicate. The optimal enterprise approach uses both: AI-powered testing runs continuously for breadth, and manual expert testing runs quarterly for depth. This eliminates the blind spot between annual pentests.
How should enterprises measure the effectiveness of their security strategy?
Track these operational metrics quarterly: mean time to detect (MTTD) and mean time to respond (MTTR) for security incidents, percentage of VAPT findings with corresponding SOC detection rules, recurring findings rate between VAPT engagements (should trend toward zero), percentage of critical and high vulnerabilities remediated within SLA, attack simulation detection rate (what percentage of red team actions did the SOC detect), and cost per security incident handled. These metrics measure whether the three pillars are integrated and improving, not just whether they exist.
An enterprise security strategy that treats VAPT, SOC, and AI as separate programs is three programs with zero integration. XHack delivers all three pillars as an integrated platform: certified VAPT and red team services, SOC monitoring and threat intelligence, and XHack AI for autonomous testing, malware analysis, exploit development, and real-time threat intelligence. Over 500 organizations trust XHack to bridge the gap between periodic testing and continuous protection.
Follow Us on XHack LinkedIn and XHack Twitter
