30-Second Summary: Small businesses are three times more likely to be targeted by cybercriminals than large companies, and 60% of those that suffer a significant cyberattack close within six months. The average cost of a breach for a small business ranges from $120,000 to $1.24 million. Meanwhile, 66% of SMBs cite cost as their top obstacle to better security, and 74% of SMB owners self-manage cybersecurity or rely on an untrained friend or family member.
Global SMB cybersecurity spending is projected to hit $109 billion by 2026 at a 10% growth rate, which means the market knows the problem exists. The gap is practical guidance on where to spend limited dollars for maximum protection. This guide breaks down exactly what cybersecurity for startups looks like at every budget level: what to prioritize first, where vulnerability scanning fits, when a real penetration test makes sense, and how to build a security posture that doesn’t require a Fortune 500 budget.
Here’s the uncomfortable math most startup founders avoid.
A basic vulnerability assessment costs $1,000 to $5,000. A proper penetration test costs $5,000 to $30,000. Security awareness training runs $3 to $8 per user per month. A managed endpoint protection platform costs $8 to $15 per device per month.
A data breach costs $120,000 to $1.24 million.
Ransomware appeared in 88% of breaches involving SMBs in 2025 (Verizon DBIR), and the average ransomware incident cost $5.08 million (IBM). Ransomware alone accounts for 51% of total cyberattack costs for small and medium businesses, and that share is projected to rise.
Cybersecurity for startups isn’t about matching enterprise spending. It’s about spending the right amount in the right places so a single incident doesn’t end your company. This guide is the practical roadmap.
Why Cybersecurity for Startups Is Non-Negotiable in 2026
The shift happened gradually, but the data is clear. Attackers moved downstream because that’s where the easy wins are.
Large enterprises invested billions in security operations centers, endpoint detection, network segmentation, and dedicated security teams. They’re not impenetrable, but they’re expensive to attack. A startup running default cloud configurations with no security monitoring and no employee security training is a fraction of the effort for a comparable payout.
70% of cyber attackers deliberately target small businesses (Cisco). Small businesses are three times more likely to be targeted than larger companies. 61% of small businesses experienced a breach in the last year. 70% of ransomware attacks hit businesses with fewer than 500 employees. The total annual cost of cybercrime to small businesses is $2.4 billion.
The attacks aren’t sophisticated. Most small business breaches exploit the basics: unpatched software, phishing emails, weak passwords, and misconfigured cloud services. The Verizon 2025 DBIR found that 20% of all breaches began with exploited vulnerabilities (meaning unpatched systems), and the human element was involved in 60% of breaches.
This is actually good news for cybersecurity for startups. If the attacks exploit basics, fixing the basics provides disproportionate protection. You don’t need a million-dollar security program. You need the right foundational controls deployed correctly.
The Cybersecurity for Startups Budget Reality
Let’s ground this in real numbers.
The IANS Research and Artico Search Security Budget Benchmark Report found that companies spent an average of 0.69% of revenue on cybersecurity in 2024 and 2025. For a startup generating $5 million in annual revenue, that translates to roughly $34,500 per year on security.
A MySecurityMarketplace study found that 29% of small companies spend less than 5% of their IT budget on security, and only 5% spend more than 20%. Meanwhile, 63% of small businesses increased their cybersecurity budgets in 2025, a sign that awareness is growing even if spending hasn’t caught up with the threat.
The problem isn’t that startups don’t care about security. It’s that security products and services are typically priced, packaged, and marketed for enterprises. A startup founder looking at a $50,000 annual security platform contract isn’t being irresponsible when they say no. They’re being rational about resource allocation.
Cybersecurity for startups requires a different approach: prioritize ruthlessly, start with the controls that block the most attacks per dollar spent, and build incrementally as revenue grows.
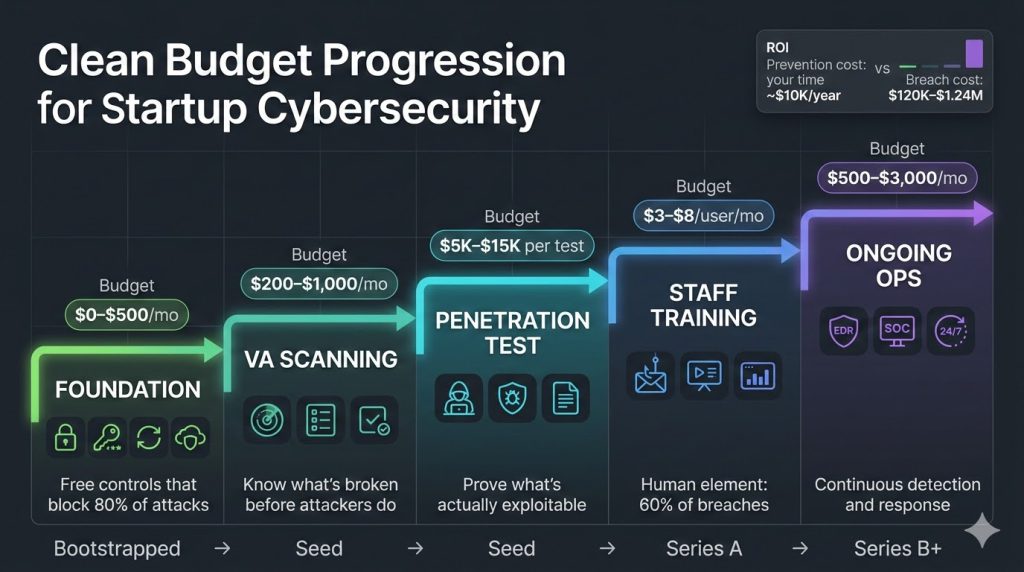
Phase 1: The Cybersecurity for Startups Foundation (Budget: $0 to $500/month)
These are the controls every startup should have in place before they spend a dollar on formal security testing. They’re cheap, many are free, and they block the majority of common attack vectors.
Enable multi-factor authentication on everything. This is the single highest-impact security control for the lowest cost. MFA on email, cloud services, code repositories, admin panels, and any SaaS application your team uses. Most platforms offer MFA for free. It blocks the vast majority of credential-based attacks, which are the entry point for most SMB breaches.
Use a password manager. Deploy a team password manager (1Password, Bitwarden) and require unique, strong passwords for every account. Cost: $3 to $8 per user per month. This eliminates password reuse, which is the reason credential stuffing attacks work.
Enable automatic updates everywhere. Unpatched software is how 20% of breaches start. Turn on automatic updates for operating systems, browsers, and applications. For server infrastructure, establish a weekly patch cycle at minimum. This costs nothing but eliminates a major attack vector.
Configure cloud services securely. If you’re on AWS, GCP, or Azure, run the free security configuration checks built into each platform (AWS Security Hub, GCP Security Command Center, Azure Security Center). Default cloud configurations are not secure configurations. Public S3 buckets, overly permissive IAM roles, and exposed database ports are among the most common findings in our assessments of startup environments.
Set up email security basics. Configure SPF, DKIM, and DMARC on your email domain. These are free DNS configurations that prevent attackers from spoofing your domain in phishing emails. Google Workspace and Microsoft 365 both provide guides for this.
Back up everything. Implement the 3-2-1 backup rule: three copies of your data, on two different media types, with one stored offsite. Test your backups monthly. Managed backup solutions cost $10 to $50 per device per month depending on data volume. This is your ransomware insurance.
These controls alone block the majority of attacks that hit startups. They’re not glamorous. They don’t require specialized expertise. And they cost less per month than most SaaS subscriptions your team already uses.
Phase 2: Vulnerability Scanning for Startups (Budget: $200 to $1,000/month)
Once the foundations are solid, the next step in cybersecurity for startups is visibility: knowing what vulnerabilities exist in your systems before an attacker finds them.
What vulnerability scanning does. Automated tools scan your systems, applications, and infrastructure against databases of known vulnerabilities (CVEs). They identify unpatched software, misconfigurations, exposed services, and weak settings. The output is a prioritized list of findings ranked by severity.
What it doesn’t do. Vulnerability scanning doesn’t prove that a vulnerability is exploitable. It doesn’t test business logic. It doesn’t simulate a real attacker. It gives you a map of potential weaknesses. Actual exploitation testing requires a penetration test (Phase 3).
Options at the startup budget level:
Cloud-native scanners (free to low cost). AWS Inspector, GCP Security Scanner, and Azure Defender provide basic vulnerability scanning for cloud infrastructure. If your stack is entirely cloud-based, these are the logical starting point.
SaaS vulnerability scanning platforms ($100 to $500/month). Platforms like Qualys, Tenable Nessus, and Intruder offer subscription-based scanning that covers external network, internal network, and web application vulnerabilities. Most offer startup-friendly pricing tiers.
XHack VA Scan. Our own platform was built specifically for this gap. It’s a secure web application where you can verify your assets, run multi-mode scans, monitor progress in real time, and generate reports tailored to different audiences: CISO-level risk summaries, developer-focused remediation details, or compliance-formatted evidence. You control your data completely, with full access to export or delete everything. No enterprise sales cycle. No annual contract trap.
How often to scan. At minimum monthly. After any significant infrastructure change. Ideally, integrate scanning into your CI/CD pipeline so every deployment is checked automatically.
What to do with results. Don’t try to fix everything at once. Prioritize by CVSS severity: patch critical and high findings within 72 hours, medium findings within 30 days, and low findings as part of regular maintenance cycles.
Phase 3: Penetration Testing (Budget: $5,000 to $15,000 per engagement)
Penetration testing is where cybersecurity for startups moves from “we know what’s potentially weak” to “we know what an attacker can actually do.” It’s the validation layer.
When a startup needs a pentest:
You’re handling customer payment data (PCI DSS requires it). You’re storing health records (HIPAA expects it). An enterprise customer or partner requires pentest results as part of vendor due diligence. You’re preparing for SOC 2, ISO 27001, or another compliance certification. You just launched a customer-facing application that handles sensitive data. You’ve completed a funding round and need to demonstrate security maturity to investors.
When a startup doesn’t need a pentest yet:
You haven’t implemented the Phase 1 basics. If MFA isn’t enabled and patches aren’t current, a pentest will just tell you what you already know: the basics are broken. Fix those first. You’re pre-product with no production infrastructure. You have fewer than five users and no customer data.
What to expect from a quality pentest at the startup budget.
For $5,000 to $15,000, you can get a focused assessment of your most critical assets: your primary web application, external network perimeter, or cloud infrastructure. This won’t cover everything, but it will cover what matters most.
A quality report will include: validated, exploitable vulnerabilities (not just scanner output), proof-of-concept demonstrations, business impact analysis, prioritized remediation guidance, and a retest to verify fixes. Be wary of any “penetration test” priced under $4,000. At that price, you’re almost certainly receiving an automated vulnerability scan relabeled as a pentest.
The ROI math. VAPT typically finds 5 to 15 exploitable vulnerabilities. If even one of those, left unpatched, would have led to a breach costing $120,000 or more, the $10,000 pentest delivered a 12x return on investment. That’s conservative math.
Phase 4: Security Awareness Training (Budget: $3 to $8/user/month)
The human element is involved in 60% of breaches (Verizon DBIR 2025). No technical control eliminates human error. Cybersecurity for startups must address the people layer, not just the technology layer. Training reduces human-caused incidents measurably.
What effective training looks like for startups. Skip the annual compliance checkbox training that nobody remembers. Deploy a platform that sends simulated phishing emails to your team on a regular basis (monthly at minimum), provides short training modules when someone clicks a simulated phish, and tracks improvement metrics over time.
Platforms like KnowBe4, Proofpoint Security Awareness, and several smaller providers offer startup-friendly pricing at $3 to $8 per user per month. For a 20-person startup, that’s $60 to $160 per month.
What to focus on. Phishing recognition (still the most common entry vector). Safe handling of credentials and sensitive data. How to report suspicious activity without fear of punishment. Basic device security for remote work environments.
The cultural component matters more than the platform. A founder who takes security seriously sets the tone. A team that feels comfortable reporting a suspicious email without getting blamed creates a security culture. A startup that treats security as everyone’s responsibility rather than “the IT person’s problem” is dramatically harder to breach.
Phase 5: Ongoing Cybersecurity for Startups Operations (Budget: $500 to $3,000/month)
As your startup grows, so does your attack surface. Cybersecurity for startups at this stage shifts from periodic testing to continuous operations. At some point (typically around 20 to 50 employees, or when handling significant customer data), you need ongoing security operations, not just periodic testing.
Endpoint detection and response (EDR). Managed EDR platforms protect every device from ransomware, malware, and zero-day threats. Cost: $8 to $15 per device per month. This replaces traditional antivirus with active monitoring and response capability.
Managed detection and response (MDR). If you can’t afford a dedicated security team (most startups can’t), an MDR provider gives you 24/7 monitoring, threat detection, and incident response for a monthly fee. This is essentially outsourcing your SOC. Cost: $1,000 to $3,000 per month depending on scope and number of endpoints.
Log management and monitoring. Aggregate logs from your cloud services, applications, and infrastructure into a central platform. Even basic log aggregation (CloudWatch, Datadog, or an open-source ELK stack) provides visibility into what’s happening in your environment.
Recurring vulnerability scanning and annual pentesting. Once you’ve done your first pentest, make it annual at minimum. Keep vulnerability scanning running continuously or monthly. Feed pentest findings back into your vulnerability management process.
The Cybersecurity for Startups Budget Matrix
Bootstrapped / Pre-Revenue (Under $500/month total): MFA everywhere (free). Password manager ($3 to $8/user/month). Automatic updates (free). Cloud security configuration (free). Email security basics (free). Backups ($10 to $50/device/month).
Seed Stage / Early Revenue ($500 to $2,000/month total): Everything above, plus: vulnerability scanning platform ($100 to $500/month). Security awareness training ($3 to $8/user/month). EDR on all devices ($8 to $15/device/month). First penetration test ($5,000 to $15,000 one-time).
Series A / Growth Stage ($2,000 to $5,000/month total): Everything above, plus: managed detection and response ($1,000 to $3,000/month). Annual penetration testing. Compliance preparation (SOC 2, ISO 27001 as needed). Incident response plan documentation.
Series B+ / Scale Stage ($5,000+/month): Everything above, plus: dedicated security personnel or fractional CISO. Quarterly penetration testing. Red team exercises. Supply chain security assessment. AI/ML security testing (if deploying AI systems).

5 Cybersecurity for Startups Mistakes That Cost You Everything
Mistake 1: Doing nothing because “we’re too small to be a target.” You’re not. 70% of attackers target small businesses. 61% experienced a breach last year. The attack isn’t personal. It’s automated. Bots scan the internet for vulnerable systems and don’t check your revenue before exploiting them.
Mistake 2: Buying an enterprise security tool instead of fixing the basics. A $50,000 SIEM is useless if MFA isn’t enabled on your email. Fix the free and cheap controls first. They block more attacks than any single expensive product.
Mistake 3: Getting a pentest before the environment is ready. If your vulnerability scan returns 200 critical findings, a penetration tester will spend their entire engagement exploiting obvious weaknesses that a $2,000 scan would have caught. Remediate scan findings first. Then pentest to validate what the scanner couldn’t catch.
Mistake 4: Treating security as a one-time project. Security isn’t a project with a completion date. It’s an ongoing operational function. A pentest from 12 months ago doesn’t tell you anything about what changed since then. Continuous scanning and recurring testing are required.
Mistake 5: Not budgeting for incident response. Every startup should have a documented plan for what happens when (not if) a security incident occurs. Who gets called. What systems get isolated. How customers get notified. How evidence gets preserved. This costs nothing to write and saves everything when you need it.
Frequently Asked Questions
How much should cybersecurity for startups actually cost?
Industry data suggests 0.69% of revenue on average, but for startups, the better framework is stage-based. Pre-revenue companies should implement the free and low-cost foundational controls (MFA, patches, backups, cloud configuration) for under $500 per month. Seed-stage companies handling customer data should budget $500 to $2,000 per month for vulnerability scanning, training, and endpoint protection. Growth-stage companies preparing for enterprise customers or compliance should budget $2,000 to $5,000 per month, including annual penetration testing. The key principle is that every dollar spent on prevention eliminates many dollars of potential breach cost. IBM’s data shows small business breaches cost $120,000 to $1.24 million. A $10,000 annual security budget that prevents one incident delivers 12x to 124x return.
When should a startup get its first penetration test?
Cybersecurity for startups reaches the penetration testing stage when you have a production application handling customer data, when a compliance framework requires it (PCI DSS, SOC 2, ISO 27001, HIPAA), when an enterprise customer requests pentest results as part of vendor evaluation, or when you’ve completed a funding round and need to demonstrate security maturity. Don’t get a pentest if you haven’t implemented basic controls first. Run a vulnerability assessment first, remediate the critical and high findings, then engage a penetration tester to validate what remains. This maximizes the value of the more expensive manual testing engagement.
What’s the difference between a vulnerability scan and a penetration test, and which one do I need?
A vulnerability scan is automated, costs $1,000 to $5,000, takes hours to days, and produces a list of known weaknesses ranked by severity. A penetration test is manual, costs $5,000 to $30,000, takes one to four weeks, and produces validated exploitable vulnerabilities with proof-of-concept demonstrations and business impact analysis. Most startups need both: continuous or monthly scanning for ongoing visibility, and annual penetration testing for deep validation. The scan tells you what’s potentially broken. The pentest tells you what an attacker can actually do with it.
Cybersecurity for startups doesn’t require an enterprise budget. It requires the right priorities in the right order. XHack works with startups and SMEs at every stage, from first vulnerability assessment through annual penetration testing and compliance preparation. Our VA Scan platform gives you self-service scanning with role-specific reporting. Our pentest team delivers focused assessments scoped to startup budgets and startup risk profiles. No enterprise pricing. No six-month sales cycle. Just clear findings and practical remediation you can act on.
Follow Us on XHack LinkedIn and XHack Twitter
